In several cybercrimes, attackers steal your online information without asking anything from you. But, here we are going to talk about a cybercrime where a miscreant can intimidate you into giving you whatever he or she wants. Here we are going to talk about cyber extortion. In the recent past, cyber-criminals have not just used cyber extortion on businesses but have even made several individuals their victims.
So, What is Cyber extortion?
Extortion is a common form of crime where a criminal applies intimidation, force, blackmailing techniques, or illegal power to get something in return. It could be some monetary gain or any other response. Now, throw in the term “cyber”. In more recent and digital terms, cybercriminals gain access to your digital data and then demand payment or any other response in return.
Let’s quickly have a look at common kinds of cyber extortion.
(i) DDoS Attacks
Here the cyberattacks flood a given network with so much malicious traffic that it can’t communicate or operate normally. This affects access to data and servers. When a cybercriminal launches such an attack, a huge amount of ransom is demanded to stop the attack.
(ii) Cyber Blackmail
In this kind of attack, cybercriminals intrude on a private network. They then steal valuable networks and keep the information residing in that network hostage. And, unless their demands are met, the cybercriminals don’t hand over the information back.
In the year 2017, two famous streaming platforms and were under a cyber blackmail attack where the extortionists released episodes when they were not paid the ransom.
(iii) Ransomware
A very popular form of malware that holds a victim’s information as a hostage and then the attacker asks for a particular ransom to leave the information free. Here users are also given a set of instructions on how they can pay the demanded fee so that the encryption on the data can be removed.
Quite recently a ransomware gang LockBit 2.0 unloaded an attack on IT giant Accenture. The threat actors stated that unless the giant paid them the ransom they would publish the data.
The Week in Ransomware – August 13th 2021 – The rise of LockBit – @LawrenceAbramshttps://t.co/93i8Z7JPkp
— BleepingComputer (@BleepinComputer) August 13, 2021
How Can You Prevent Yourself From Cyber Extortion?
1. Use A Password Manager
There are several instances of passwords being compromised. One of the ways to ward off cyber extortion is to use strong passwords. Under normal circumstances, we often use passwords that can be easily compromised. And, for hackers, it is an easy task to find out passwords especially if they are easy to decipher. Once a hacker knows your password he or she can threaten you to furnish whatever data they want.
Knowing the fact that it is next to impossible to remember long passwords for all your accounts, you can always take the aid of a robust password manager which is capable of delivering unique and strong passwords for each of your accounts.
Here is a list of some of the best password managers. TweakPass doesn’t just safeguard your passwords but does a lot many things to strengthen your online security. Here are some of the core functions of TweakPass –
Click Here to Download TweakPass
Features of TweakPass
- TweakPass stores all your passwords at a single location that can only be accessed by you
- AES-256-bit encryption
- A strong password generator helps generate long, secure passwords that fulfill the condition for a strong password. For instance, it ensures that a password has upper case and lower case characters, numbers, symbols, etc and if the password is complex enough
- You can sync stored passwords across all devices
- You can save passwords and logins as you browse
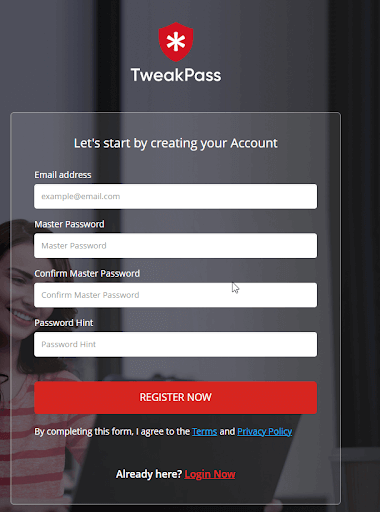
How to Use TweakPass
Want to see TweakPass in action, do check out this post. However, let’s get you started, shall we?
- Visit tweakpass.com and then click on the hamburger icon located at the right-hand side of the page and click on Downloads
- Select the platform on which you want to install TweakPass. You can download TweakPass as an extension on your browser or install it on your computer or smartphone
- Let’s say you have installed TweakPass on your Windows computer. Run the installer by double-clicking on the setup file
- Sign-up for an account. Here you will be entering your email ID and creating a Master Password
- That’s it, follow the on-screen instructions and you are all good to go.
Must Read: Best LastPass Alternatives To Manage Your Passwords
2. Use 2 Factor Authentication
Two-factor authentication is considered one of the best and the most powerful ways to protect online information. It acts as an extra layer of protection beyond the username and password that you provide while signing up.
For instance, here you might be sending a 6 digit code that you may have to enter after you have signed up using username or password or you might have to tap or click on the ‘yes’ button.
The best part is that these actions can only be performed by you (unless someone has stolen your device from you).
3. Avoid Clicking On Links
Regardless of whether you are using official or personal email, you should never click on suspicious links which may appear to come from a reputable source. For example, you might receive a fake email from PayPal or any other banking website that your account has been compromised and you might be asked to furnish details like credit card number, bank account details, CVV, OTP, etc. Never trust such websites because no official from your bank would ever send you any such email.
To know more about how you perceive if someone is phishing you, you can check out this post.
4. Keep Your Devices To Yourself
Whether it be your friend, colleague, or relative, you should restrain others from using your devices such as computer, laptop, mobile, or any other device, especially those devices that may contain your personal information.
One of the elements based on which a person can intimidate you or extort things from you is when he or she has information about you that can be compromised.
5. Update Your Operating System and Software
Software and applications that haven’t been updated in a long time are one of the easiest targets for hackers. They can easily hack into unpatched vulnerabilities, steal your data and thereby intimidate you to pay up. So, it is advisable that you regularly check your operating system for any pending updates and also, make sure that all the applications on your devices are updated.
6. Install an Effective Antivirus and Maintain a Robust Firewall
The importance of firewall and antivirus, whether at an individual level or organizational level can’t be stressed enough. Modern antivirus programs are created in such a manner that no malware can get past the protective shield created by them. Antivirus software nips a malicious threat right in the bud before it can extend to the files on your computer or even to your complete computer. Here’s everything you need to know about enabling (and even disabling) a firewall on your computer.
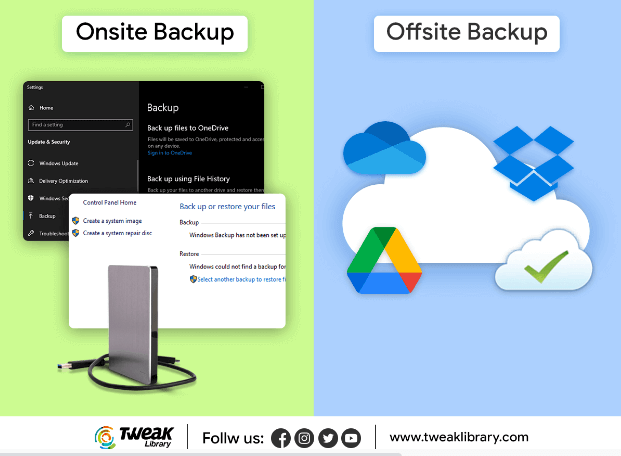
7. Create Multiple Data Backups
Whether at the organizational level or personal level, data backups should be kept at multiple places so that if data at one place is compromised, you would at least have several backups to fall back on. You can either create a backup using the facility that your operating system provides you, for instance, Windows users can use Windows 10 enhanced file history feature and Mac users can use time machine. However, you can even opt for specialist utilities to backup data on Android, Windows, and Mac conveniently and swiftly
Wrapping Up:
In this digital era, on one hand, as devices and applications make tasks more and more convenient for us, on the other hand even cybercriminals are getting benefitted. We hope that these simple steps would help you stay miles ahead of danger like cyber extortion. If you liked the information in this blog, do give it a thumbs up. We’d also love to have your inputs on how you can stay safe from cyber extortionists. Do drop in your suggestions in the comments section below.








Leave a Reply