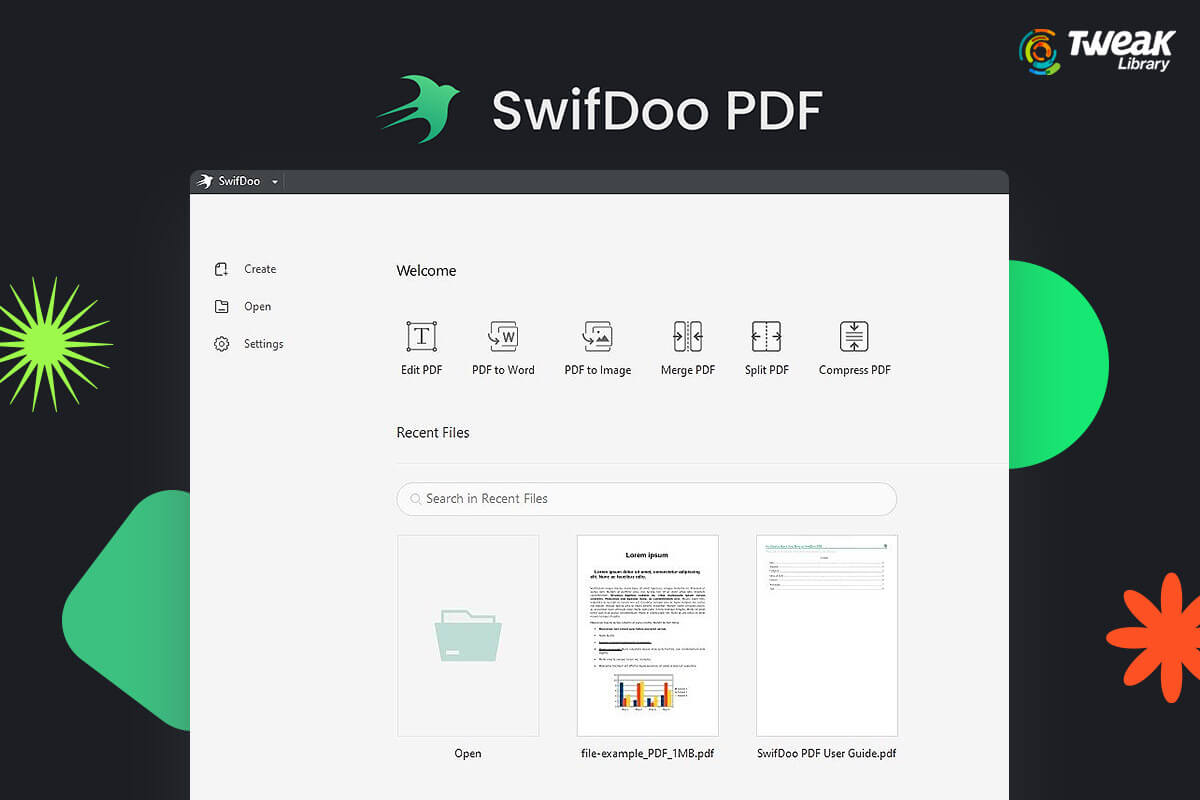
PDF is probably one of the best ways to access a document. It is reliable, and secure, and helps you include every element that you would want to make...
To expand an online business, ensure you're doing everything correctly, you need to be competent. But, sometimes you may do everything perfectly and s...

Adding page numbers is an easy skill that can make your life easy when you are reading PDFs or creating PDFs right from the scratch. And, did you know...

Through their proprietary technology, Bright Data collects structured and unstructured data from millions of websites. Using their proxy networks, you...
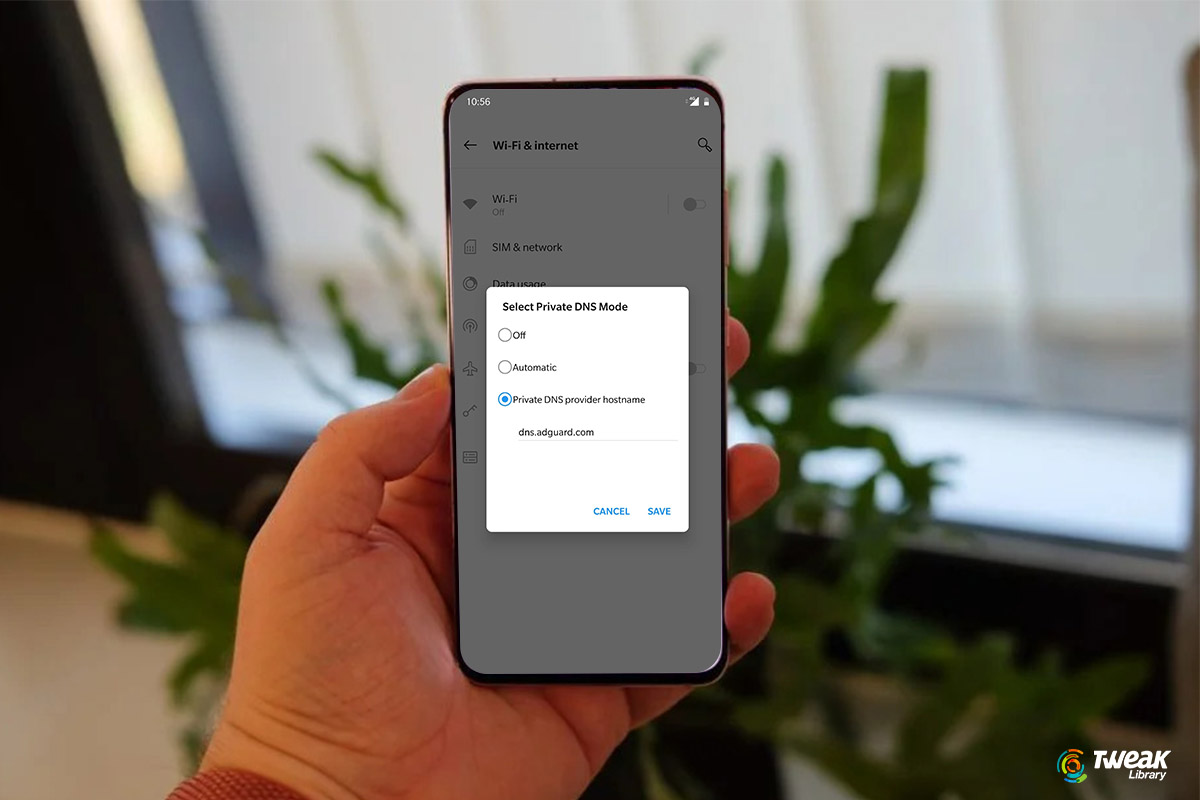
The Domain Name System (DNS) is essential to your online communications. Upgrading to a better DNS server is the right decision if you face connectivi...
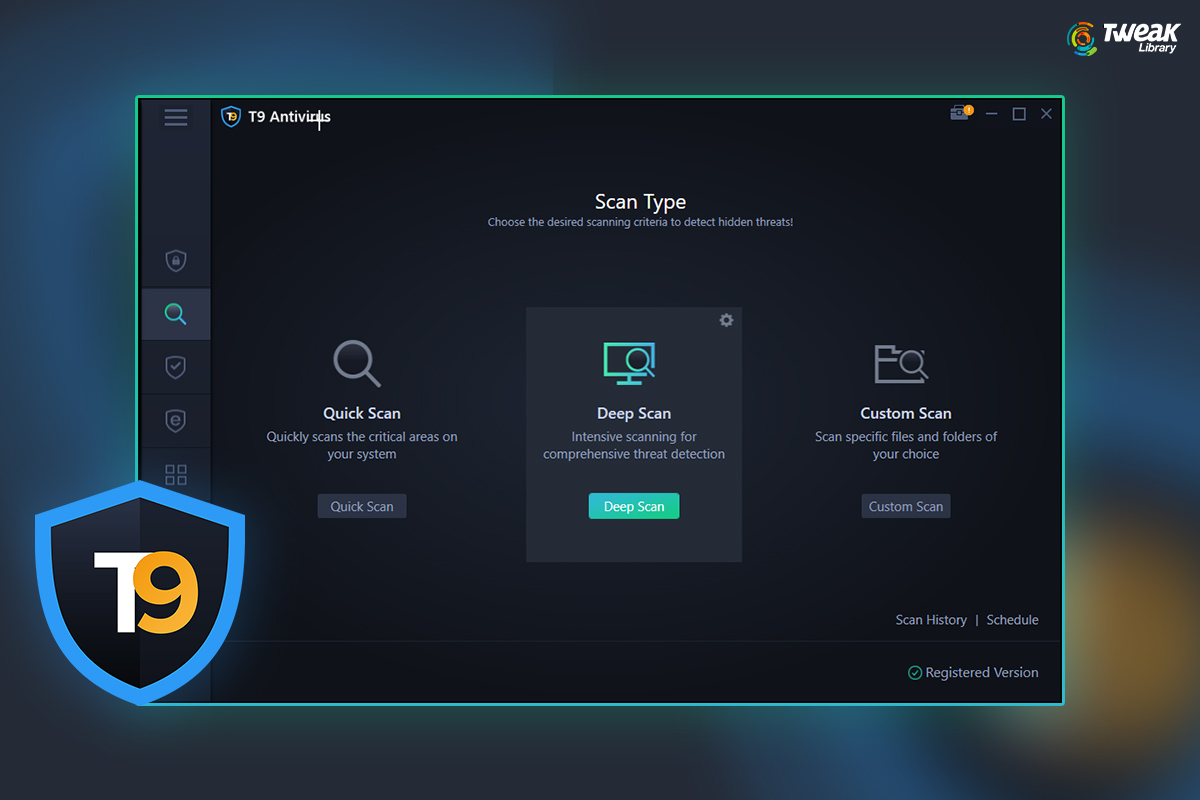
Keeping PC and data secure from cyberattacks, viruses, malware, adware, and other nasty threats have become necessary. In this regard, Tweaking Techno...

The most typical request from video producers is to remove unpleasant noises like rumble or hum from a finished video, whether a corporate piece, a sh...
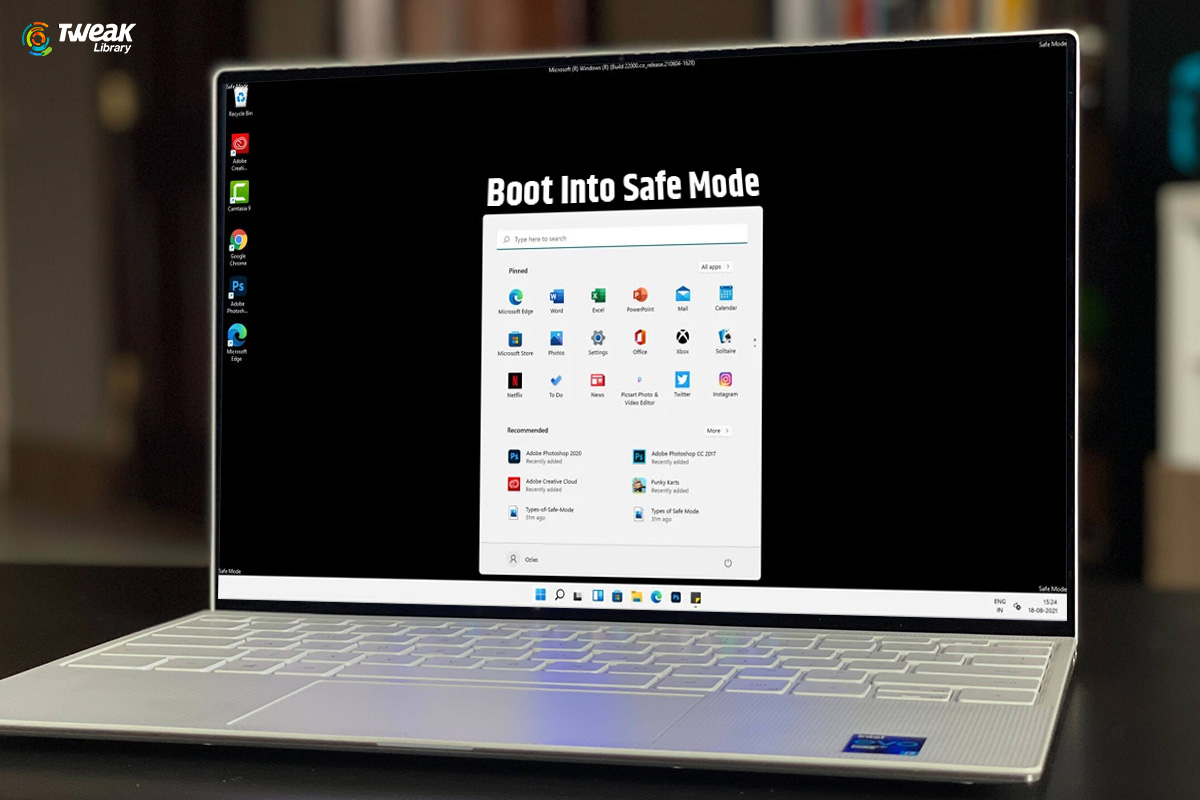
Safe Mode is a Windows diagnostic mode that starts Windows with essential system files and drivers to function in basic state. Safe Mode is typically ...

Optimizing your Mac regularly is one of the things that you could do to keep it running smooth and fast. However, doing it manually could be tedious a...

The notion of a paperless workplace is environmentally benign, and it ensures that critical information is stored efficiently. Whether for office work...
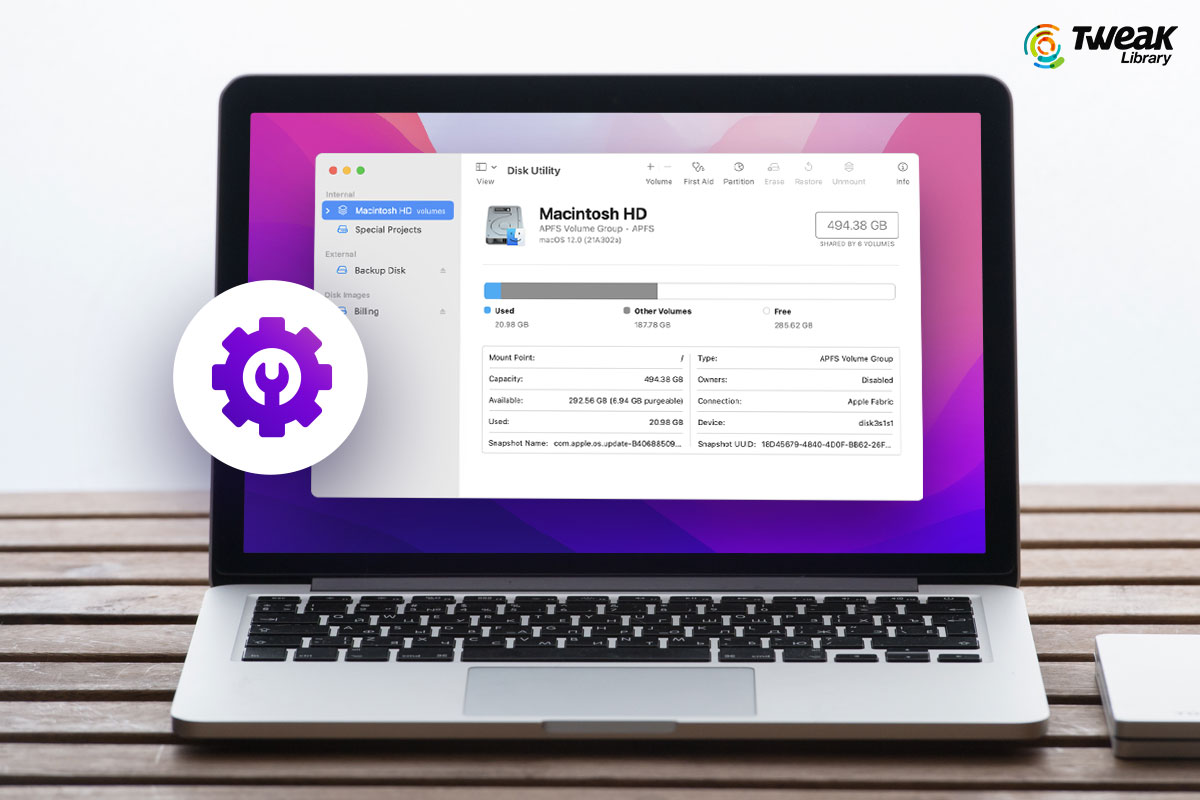
Is your Mac significantly slow? Do you frequently suffer crashes that result in data loss? Has one of your storage devices suddenly stopped working? P...
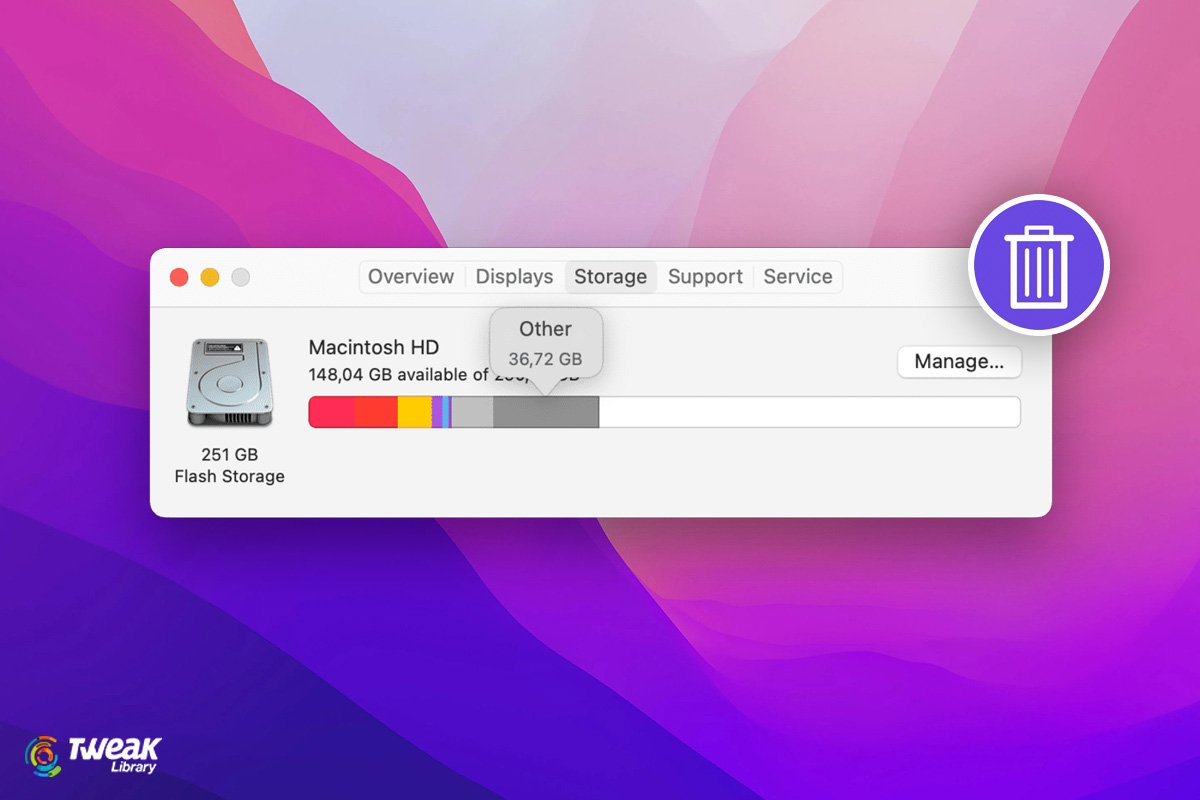
Your Mac's storage capacity is limited, especially if you have a 128GB or 256GB SSD. When your storage is nearly complete, your Mac may begin to slow ...