
The Internet has become an inseparable part of our lives. Many of us use Wi-Fi as a way to access the internet and more so, quite a many users work on...
Search indexing helps make the file searching capability faster. The Windows search indexer indexes files for the search. This means all files’ prop...

Many times users are not at home in a peaceful environment and they have to make FaceTime calls to family and friends or they have to attend some urge...

Most of us use our Android smartphones as a primary source of taking and sharing pictures. But, what we often ignore is the fact, is privacy. For ins...

Out of the many spectacular features that were introduced in WWDC 2021, one feature that has especially got users interested is the SharePlay feature....

Why have contacts on my laptop or desktop when I can have my accounts backed up on Google instead? In fact, as an Android user, you might already be a...

Finally, the wait is over and Apple has rolled out iOS 15.1. After the release of iOS 15 in September, users have been facing some bugs issues which a...

The digital world has opened all portals of convenience. And, while we are happily enjoying its convenience - browsing the internet, accessing applica...

There are several reasons why you would want to upgrade Windows 10 to Windows 11, one of which is the support for Android apps, a sleeker interface, a...
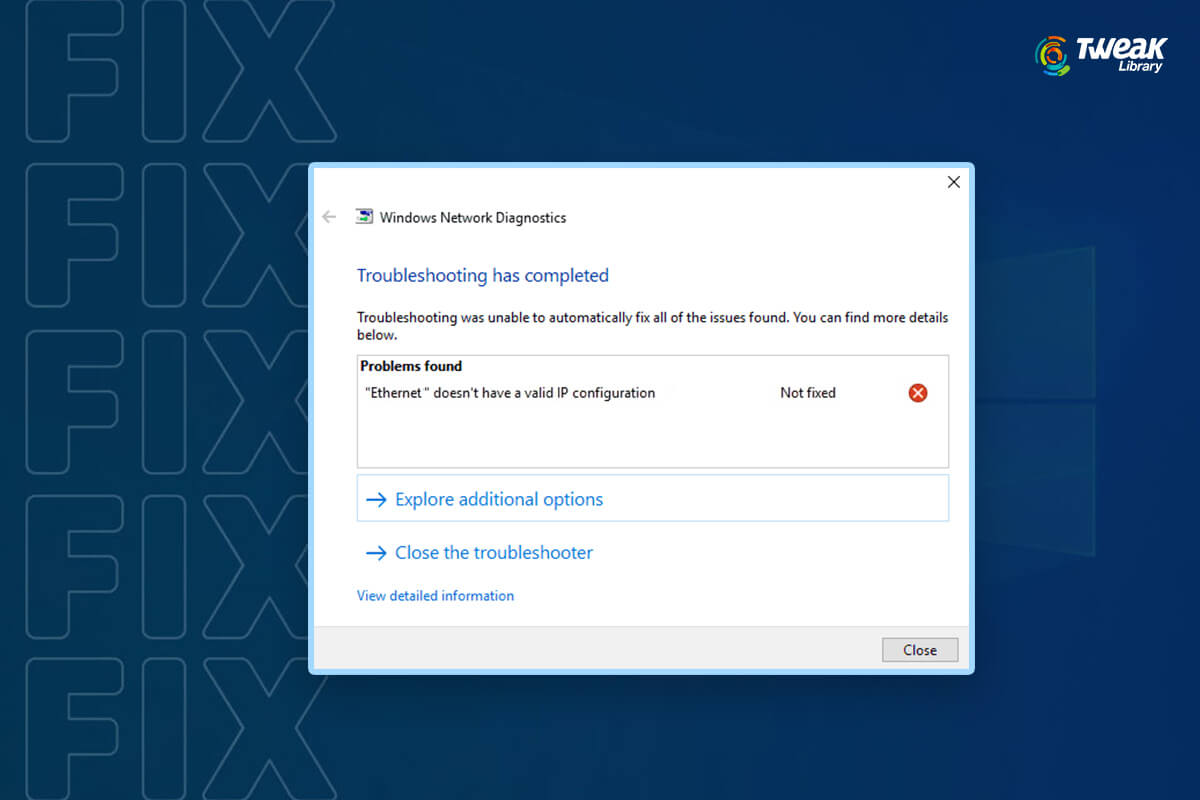
As much as we love using Wi-Fi, we are of the notion that a wired connection can provide you with even better connectivity. Which side are you on - Wi...

There are various features of the iPhone and iPad which are not found in any other phone. What can not be done through an iPhone? It is faster than ex...

The wait is finally over for all Mac users who are waiting to upgrade their machine to the latest macOS Monterey. Apple's event which took place on 18...