
In the digital world, there is content everywhere, and capturing everything seems impossible. Not anymore! Whether you want to record a lecture or pr...
No power in the whole universe can challenge the fact that the brain is the most important organ of our body. It is also the most complex organ. It co...
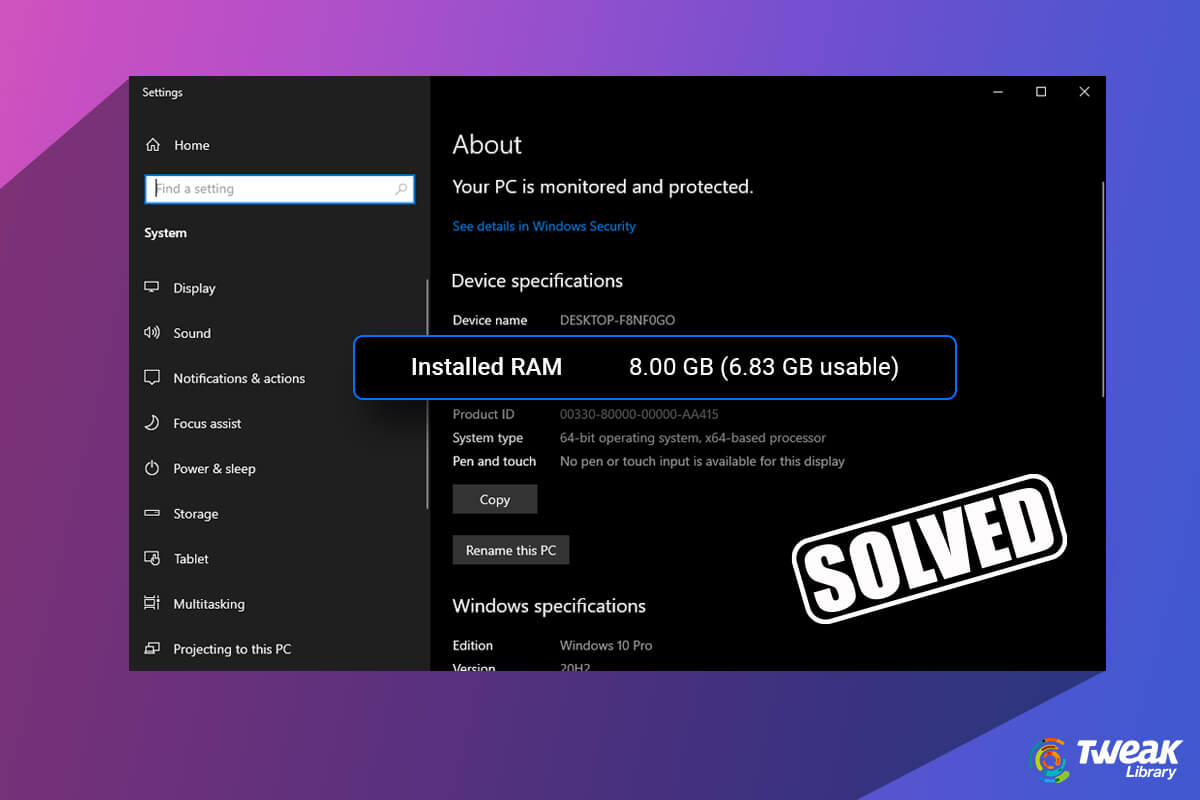
The RAM or Random Access Memory is a volatile storage medium that stores your machine code and working data. It is also the short-term memory of your ...

iPhones are known for their high-quality camera which can shoot and record high-end videos. All the users who own iPhones with good storage generally ...

There might be several instances when you might consider Factory resetting your Android device. It is important to note that after a factory reset all...

Malicious add ons and extensions somehow make way into even the world’s top-class browsers. But, what’s more important is how promptly action is t...
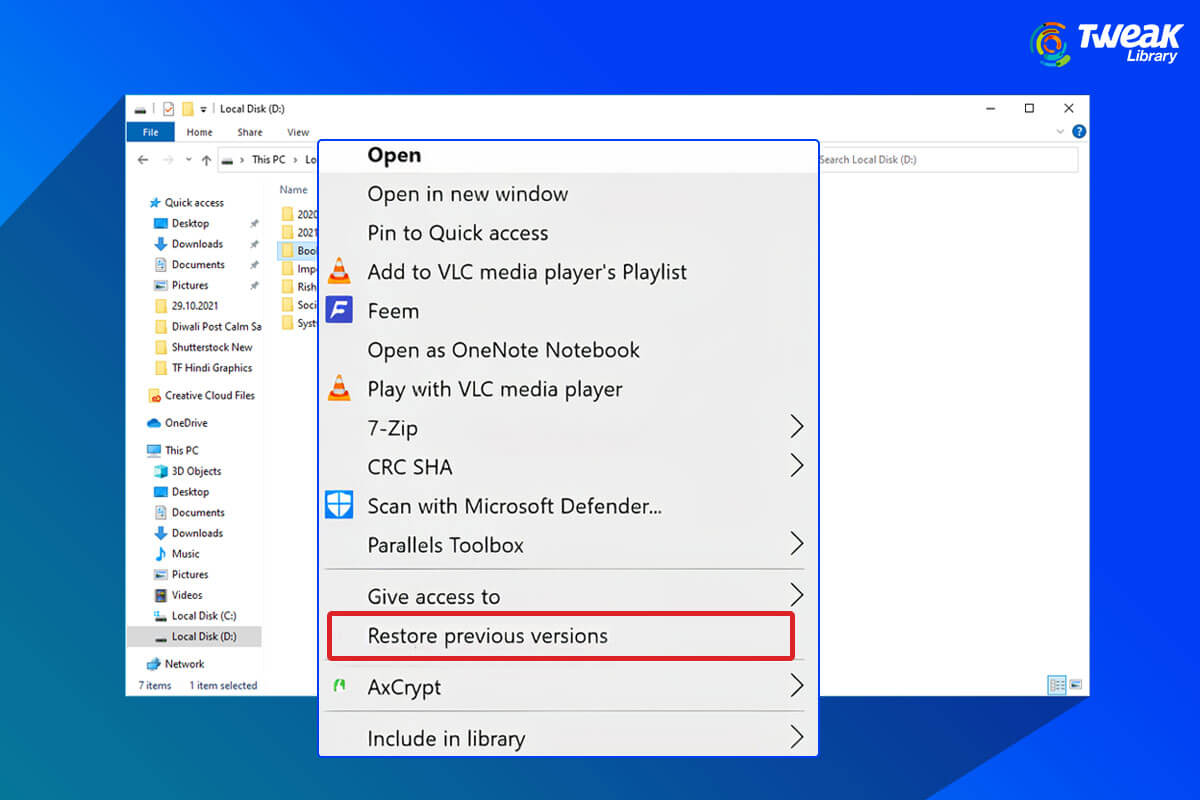
Has it ever happened that you made some changes in your current files - edited a photo/ video, made changes to a word document, and later realized it ...
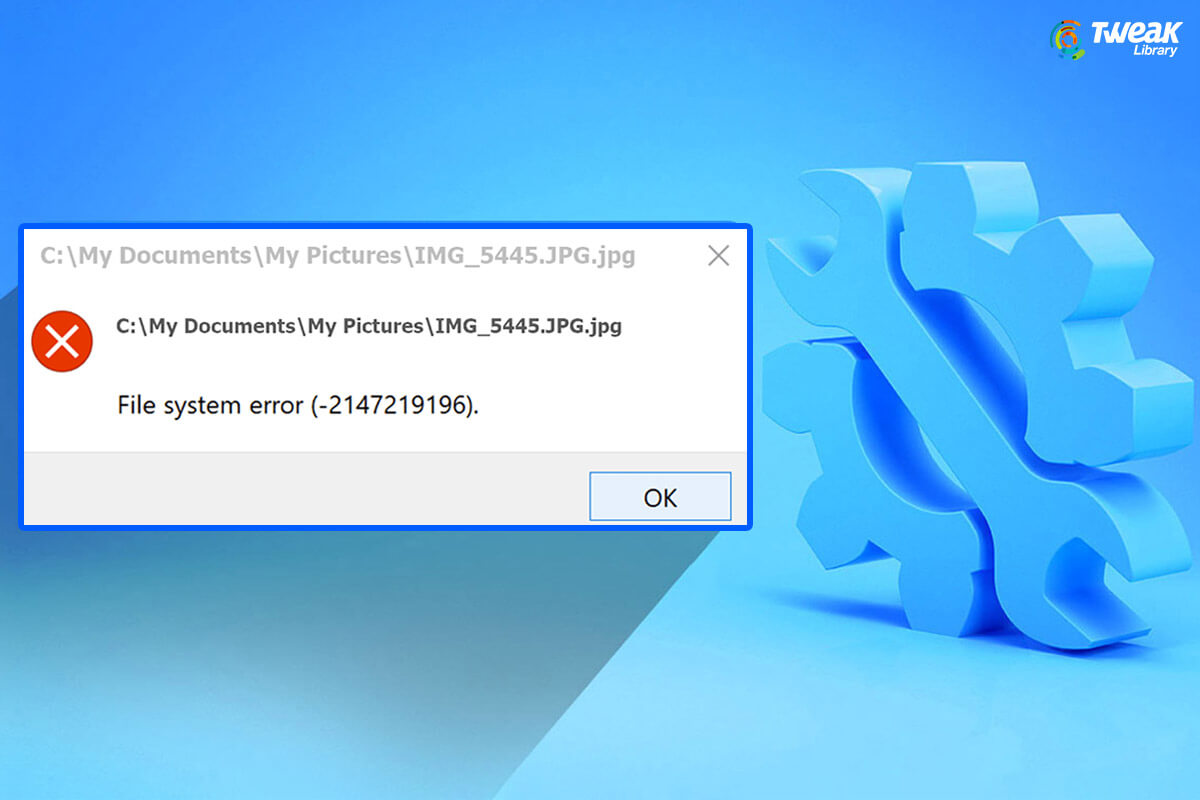
File System Errors are known to create trouble for many users. They come in various forms. Common file system errors include - the file system error (...
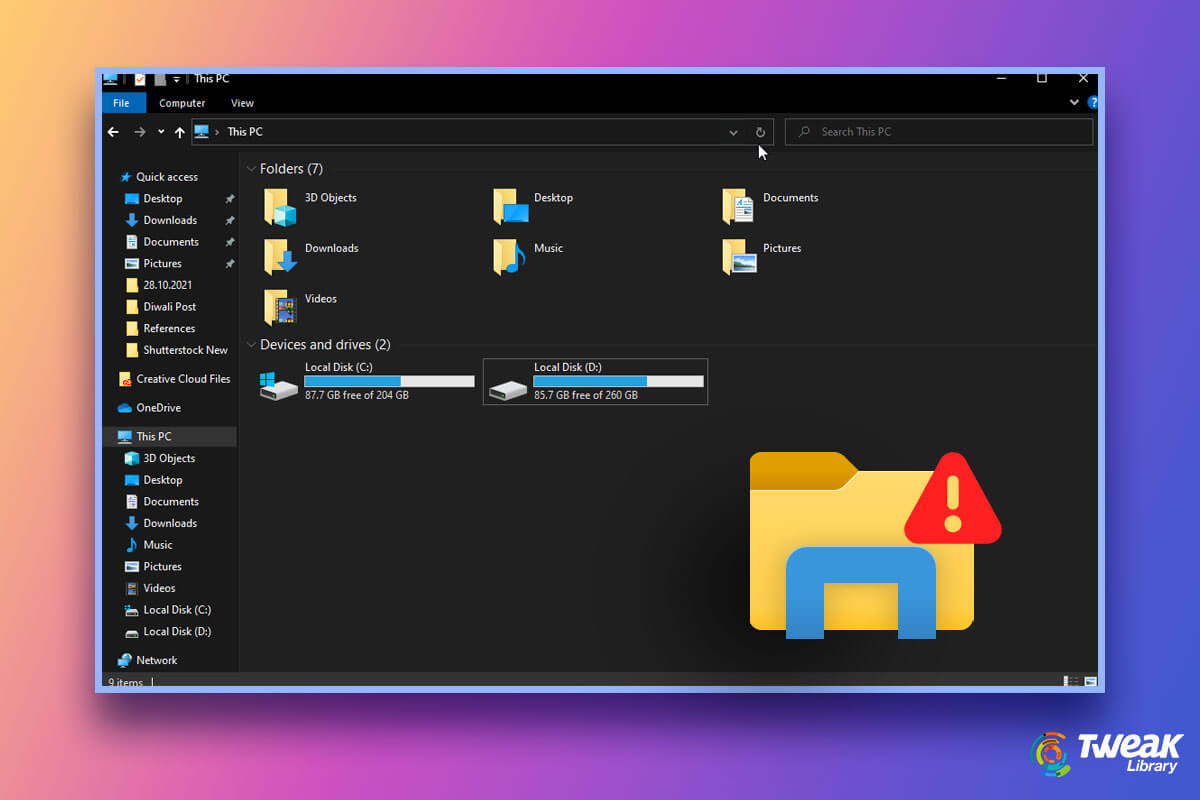
Windows Explorer popularly known as File Explorer is an important aspect of your Windows 10 computer or laptop. In simple terms, it is the place where...

Windows 11 Windows Explorer or File Explorer is more modern in look and feel. It has more modern icons, a refurbished context menu, and much more. Don...

So, you have finally got your hands on Windows 11 and you want to flaunt the new UI in front of your friends who are probably stuck with Windows 10. O...
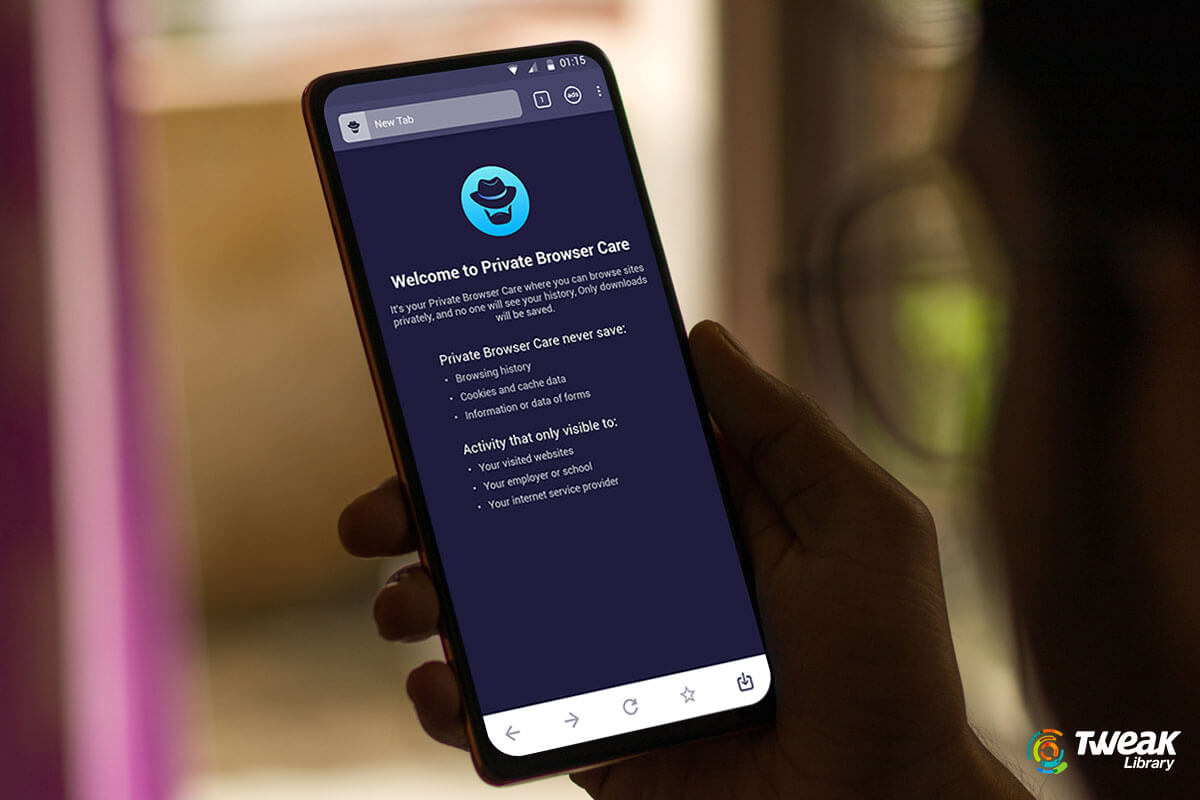
Almost all major browsers offer private browsing mode or something that’s quite popularly known as incognito mode. It has been around for quite some...