Malicious add ons and extensions somehow make way into even the world’s top-class browsers. But, what’s more important is how promptly action is taken against these. Because let’s face it, hundreds and thousands of users download such addons. If these extensions are allowed to persist, they can cause some serious hazards both in terms of security and functions.
Mozilla’s Rachel Tublitz and Stuart Colville said in a post that Mozilla recently blocked two malicious add ons on its Firefox browser. The two malicious extensions are named Bypass and Bypass XM. These abused the Proxy API and thereby prevented updates from being downloaded on the browser. The add-ons were installed by 455,000 users.
How These Malicious Firefox Add-Ons Exactly Worked?
The add-ons in question misused the proxy API, something that APIs utilize to control how the browser connects to the internet. The add-ons interfered with the Firefox browser in such a way that it stopped users from downloading any updates, some of which were necessary from a security perspective. Not just that the addons even updated content that was configured remotely. Because of these add-ons, the users were even refrained from accessing the updated blocklists.
How Mozilla Tackled These Malicious Firefox Add-ons?
To begin with, Mozilla has blocked these malicious addons. This will further prevent the installation from other users as well. It has also deployed a system add-on called Proxy Failover. This system add-on ships with further mitigations and is capable of addressing any further issues.
Mozilla Advice To Firefox Add-on Developers
Mozilla has also advised Firefox add-on developers who require proxy API for their addons to include strict_min_version key in their manifest.json files targeting browser version “91.1” or above. For example :
“browser_specific_settings”: { “gecko”: { “strict_min_version”: “91.1” } }
How Would This Help The Developers?
When a developer was set this explicitly, it would become easier to review the add-on and in turn, this would help maintain the user’s security.
How Can You Prevent Yourself From Falling Prey To Malicious Add Ons
1. Keep Your Browser Up To Date
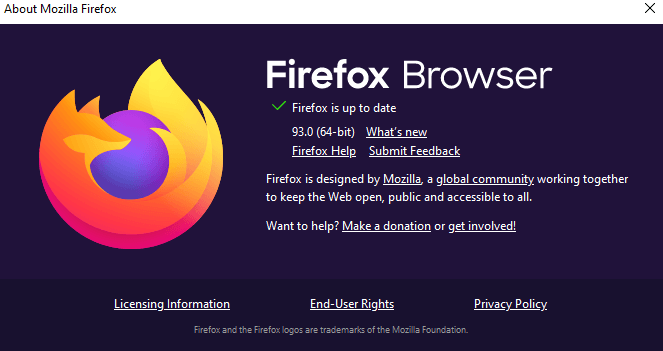
Because as is quite evident from the above case, the makers make sure that all such security flaws are poached with security updates. As a Firefox user, you should be running Firefox 93 or Firefox ESR 91.2. To check what version you are running, here are the steps –
1. Click on the menu button
2. Click on Help
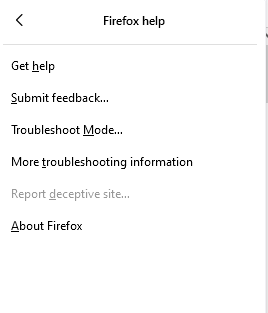
3. Choose About Firefox. You will now be able to see the version underneath the name Firefox Browser
2. What if I Have Installed The Add-On?
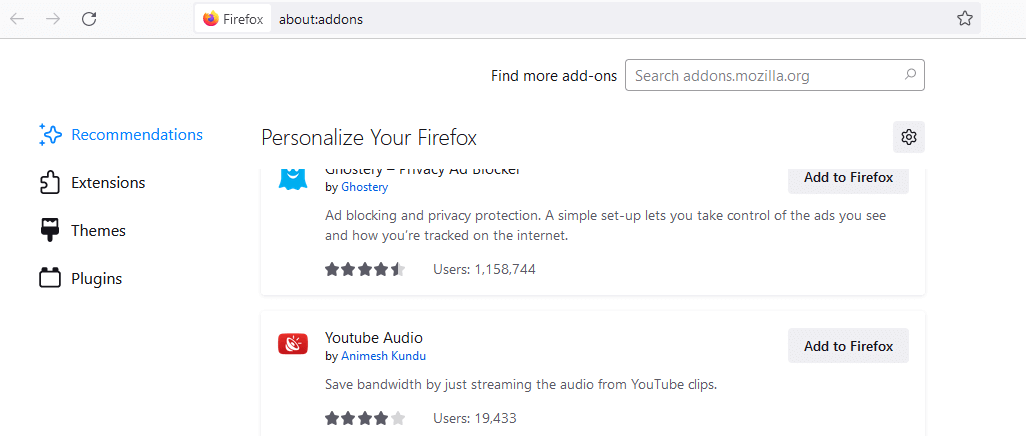
If you have installed the malicious add-ons in question, it is advisable that you remove them without further ado. To do that visit your Add-ons section and search for the following codes:
Bypass – ID: 7c3a8b88-4dc9-4487-b7f9-736b5f38b957
Bypass XM – ID: d61552ef-e2a6-4fb5-bf67-8990f0014957
As an additional step, users are also advised to refresh the Firefox browser or reinstall it completely.
3. Be Wary Of The Add-Ons You Are Installing?
Always stay away from malicious add-ons. But how? Before installing an add-on, as a prudent user make sure you see the rating, the number of downloads, comments from other users and most importantly keep your eyes and ears open to know if the add-on you have downloaded has been in news for all the wrong reasons.
Wrapping Up
As in any case, developments take place in browsers too. But not all of them could be positive. It is important on a user’s part to be informed of these developments. If you liked what you read, give this blog a thumbs up and for more such content keep reading Tweak Library.






Leave a Reply