PC and other smart devices have become an inseparable part of the lives of most people around the world. We rely on them for work, entertainment, to everything else possible. Like everywhere else, there are people who are constantly looking for opportunities to take advantage of the vulnerabilities of these systems. The good news is, there is a software to protect us from these cyber threats named Antivirus. To understand how antivirus protect our devices and data, we need to first understand the ways by which intruders can take advantage of the weak-links in our system.
Threats posed to our Systems:
Every system in the world has some inherent weaknesses that allow intruders to take advantage of users’ data. There are multiple methods (Worms, Trojans, Ransomware, Keylogger, and many more) used by intruders to do so.
Initially, these methods were inherently simple. But as time progressed and people became smarter, these hackers started coping up too and started to build Viruses and malware that are difficult to even detect, forget eliminating. They now can sneak into our system in any downloadable format, be it an MP3 file, image file, or any software or by attaching them to any legitimate file. Once a user downloads such a file into the system, it tries to steal, delete, and lock your data, to fetch money out of your pockets, one way or the other.
For example, Ransomware is one of those methods, which when enters your PC, locks all the files and folders present in the system with strong unbreakable codes. Ransomware is targeted against people who have data of importance on their devices.
There are multiple other techniques used by intruders these days, apart from Viruses, such as phishing and adware to abuse unprotected systems and files.
How does an Antivirus work to offer protection from such threats?
Like Viruses and malware, Antiviruses don’t rely on a single technique either. An antivirus has to have different techniques to try and catch the malicious files and viruses from entering the device. The techniques involved are subjective and hence, not all antiviruses offer identical protection from threats and Viruses. There are a number of techniques used by every admirable antivirus in the market. Let’s look at a few:
- Heuristic Analysis: Every virus has its signature in codes which makes the viruses distinguishable from other files. Every antivirus has a database of such signatures that have ever been used to quickly identify a malicious file. The heuristic analysis suffers a weakness from new viruses created. Because the signatures of these viruses are not present in its database. Hence, most antiviruses keep getting new updates every few days to deal with the shortcoming.
- Rootkit Detection: Rootkit is a kind of software that is designed to gain and provide access to one’s system to hackers while keeping its presence on the system a secret. Rootkit detection is a type of scan performed by the antivirus to exterminate any rootkit present in the system.
- Permission Detection: Many of the Viruses created in the early days simply relied on getting various permissions in a device while hiding behind the veil of a legitimate email or application. Once permissions were granted, they were misused to keep track of user’s activities and online transactions. This technique aims at identifying these permissions being misused.
- Sandboxing: Sandboxing is a technique employed to prevent viruses from moving into the system with the help of a software. Many time hackers disguise viruses in the form of software. Such software, when installed, harm the user’s device and data. Antiviruses eliminate this risk by first installing every software in complete isolation inside the system where if it misbehaves, is deleted by the antivirus. This technique is known as sandboxing.
There are many other techniques employed by the antiviruses to protect the device from Viruses and people with malicious intent. But as mentioned earlier, not all antiviruses offer equal protection to your device. One should always look for an antivirus that offers all-round protection from threats be it offline or online. One of the most efficient antiviruses available in the market is Systweak Antivirus.
Click Here To Download Systweak Antivirus
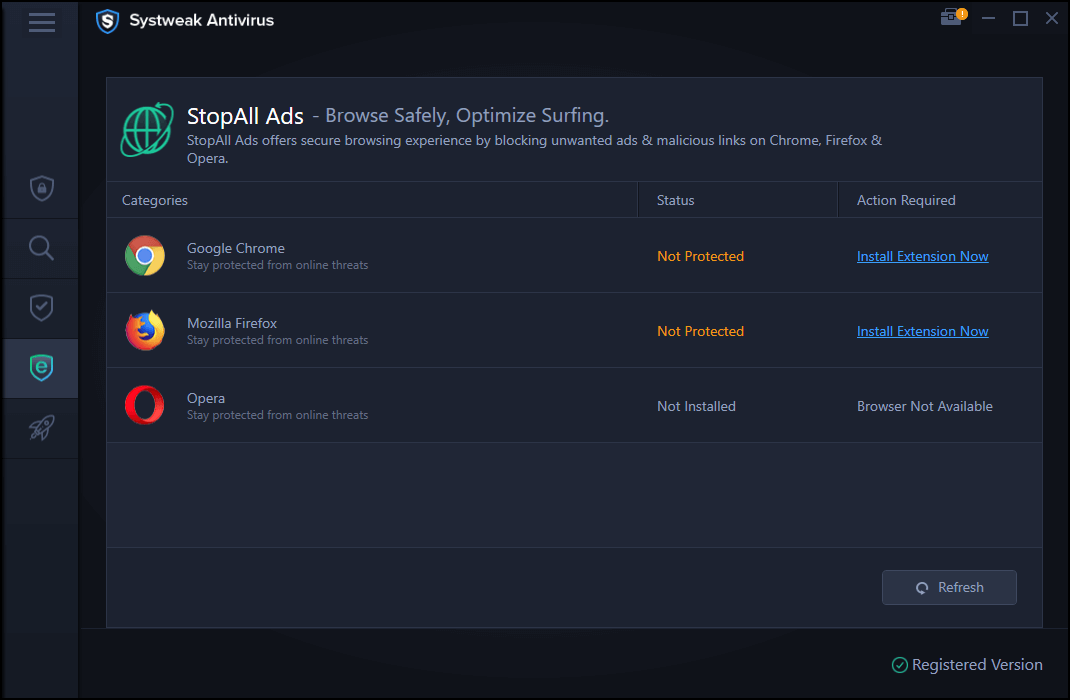
Systweak Antivirus is simply the most reliable and intuitive antivirus available in the market. It offers unmatched protection from all kinds of malware and viruses. Systweak Antivirus provides real-time protection from phishing and adware scams to keep provide unmatched online security. Let’s look at some of its features:
- Exploit and Malware Protection: Systweak Antivirus offers unrivalled protection from Malwares, Viruses, zero-day threats, PUP, and Trojan.
- Real-Time Protection: It comes equipped to provide real-time protection. It helps in instantly detecting and eliminating threats like viruses, adware, and malicious apps before they can provide any harm to your data and system.
- Scanning and removal of Malicious startup items: It also aids in neutralizing multiple startup threats to keep your system safe.
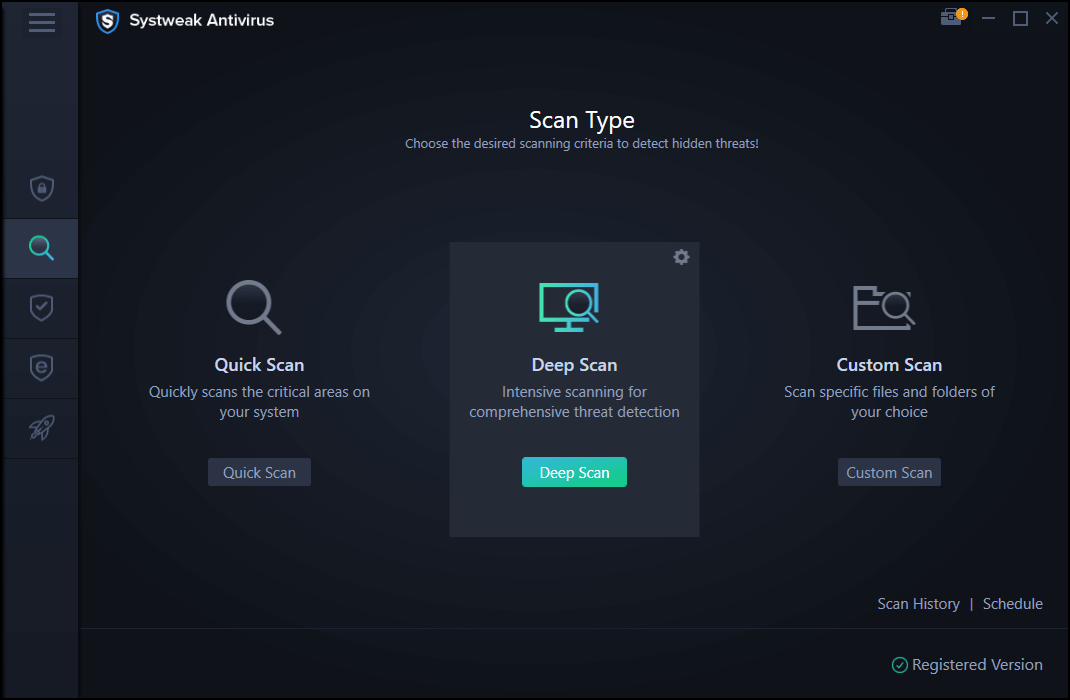
- Various Scanning options: Systweak Antivirus offers 3 different scanning options, Quick Scan, Deep Scan, and Custom scan. Multiple scanning options help meet the need of the day.
With all the above-mentioned features and more on board, we can simply suggest Systweak Antivirus be the safest and most advanced antivirus available in the market.
We hope we were able to help you with the explanation of how an antivirus keeps your system safe from many online and offline threats with just a few clicks. Do let us know what you think of Antiviruses, we love listening to your views.
Next Read
Best Antivirus For Windows 10 (Free & Paid)
Why You Should Choose An Antivirus For Android







Lucy Taylor
Big thank you for this amazing informative write up. Antivirus much needed to protect our information from hacker.