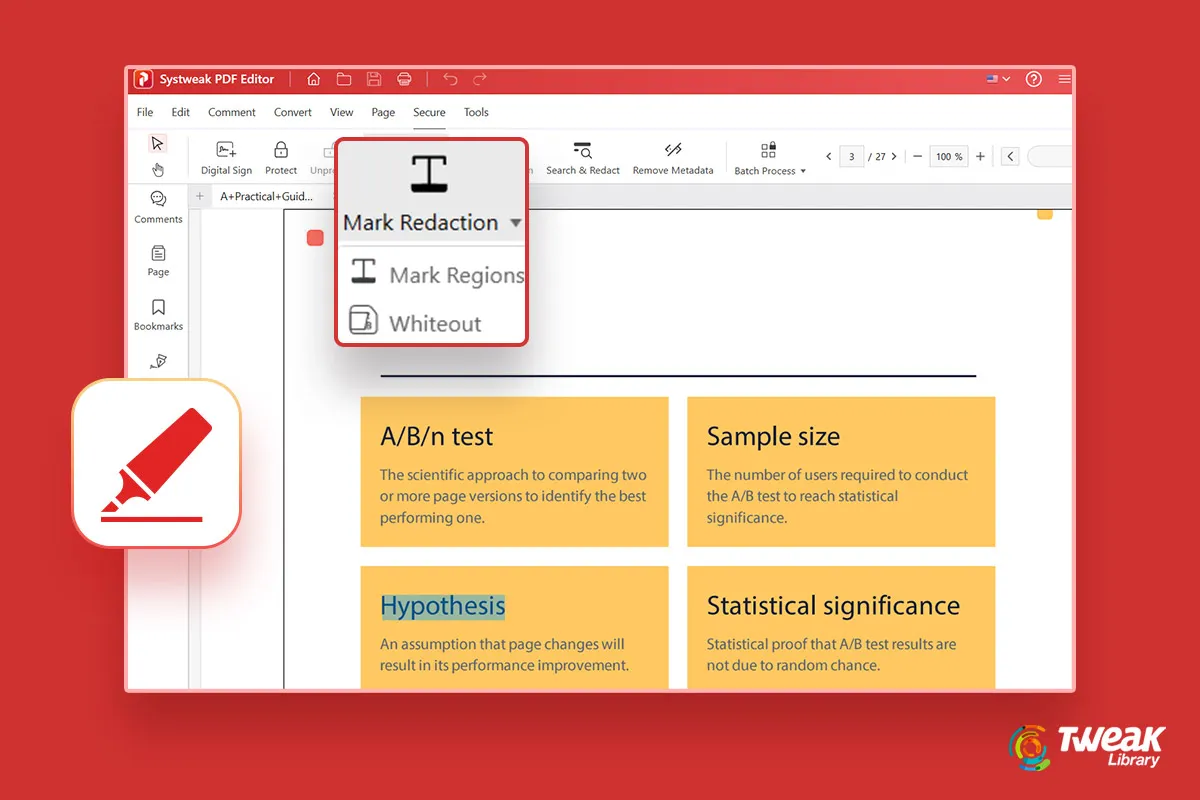
Under normal circumstances, you might use a PDF to read information. But, there are instances where things may stretch out beyond normal reading. Cons...
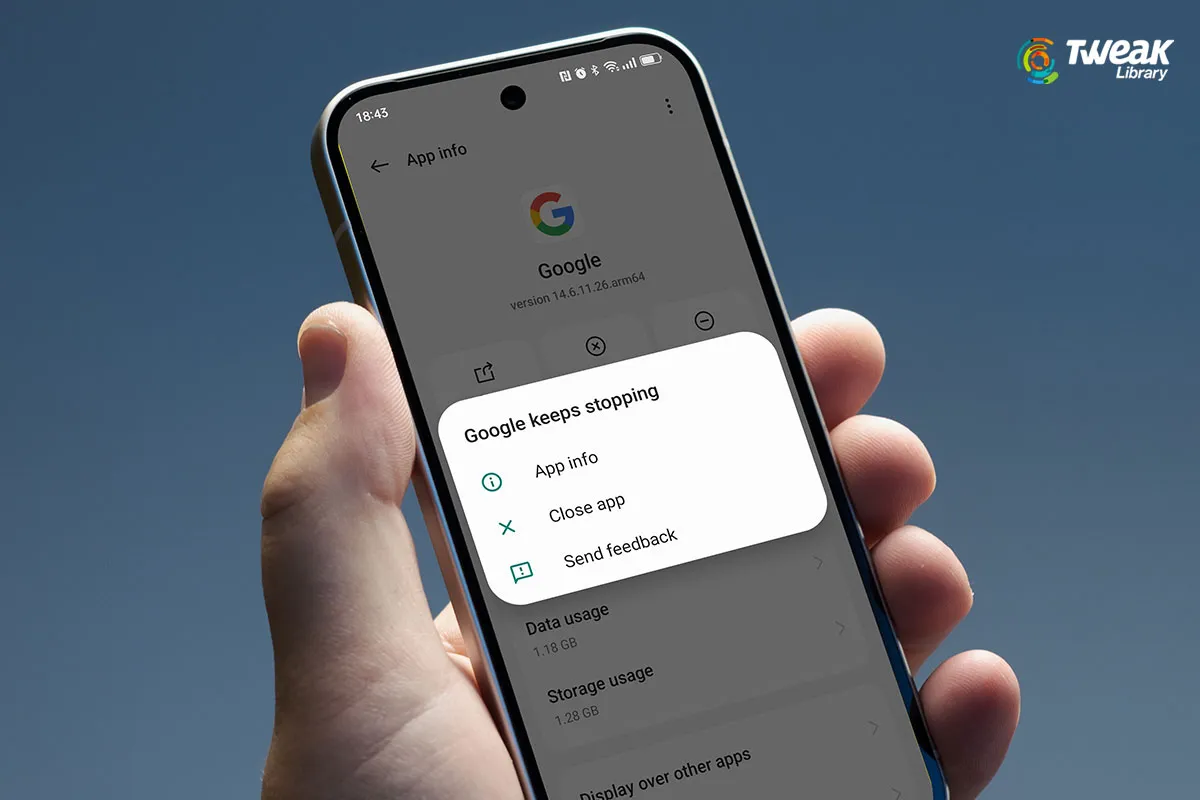
The “Google keeps stopping” error can occur anytime: When you are browsing the web using the Google Chrome browser, Downloading an app via the Goo...
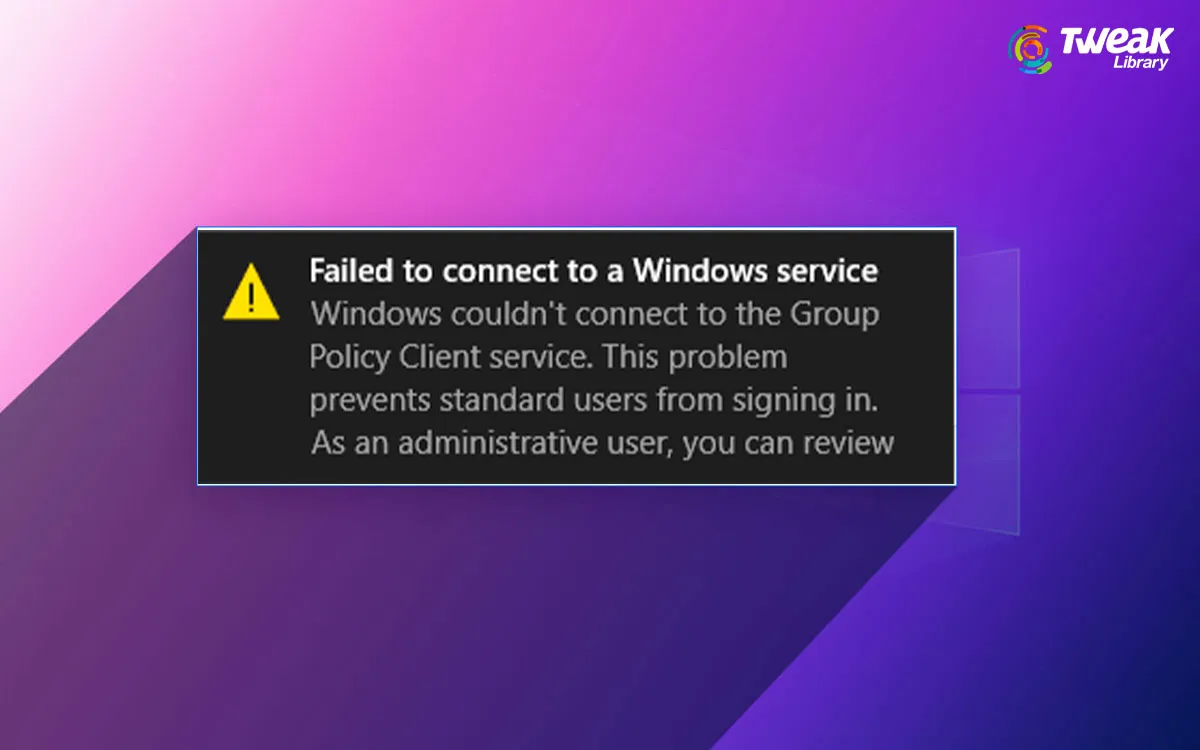
The “Failed to connect to a Windows service” error typically occurs when you are unable to connect to a Windows service on your PC. For example, y...

The keyboard is such an integral part of any iOS user’s life. In a day, you probably work your way through WhatsApp texts, send emails, create lists...
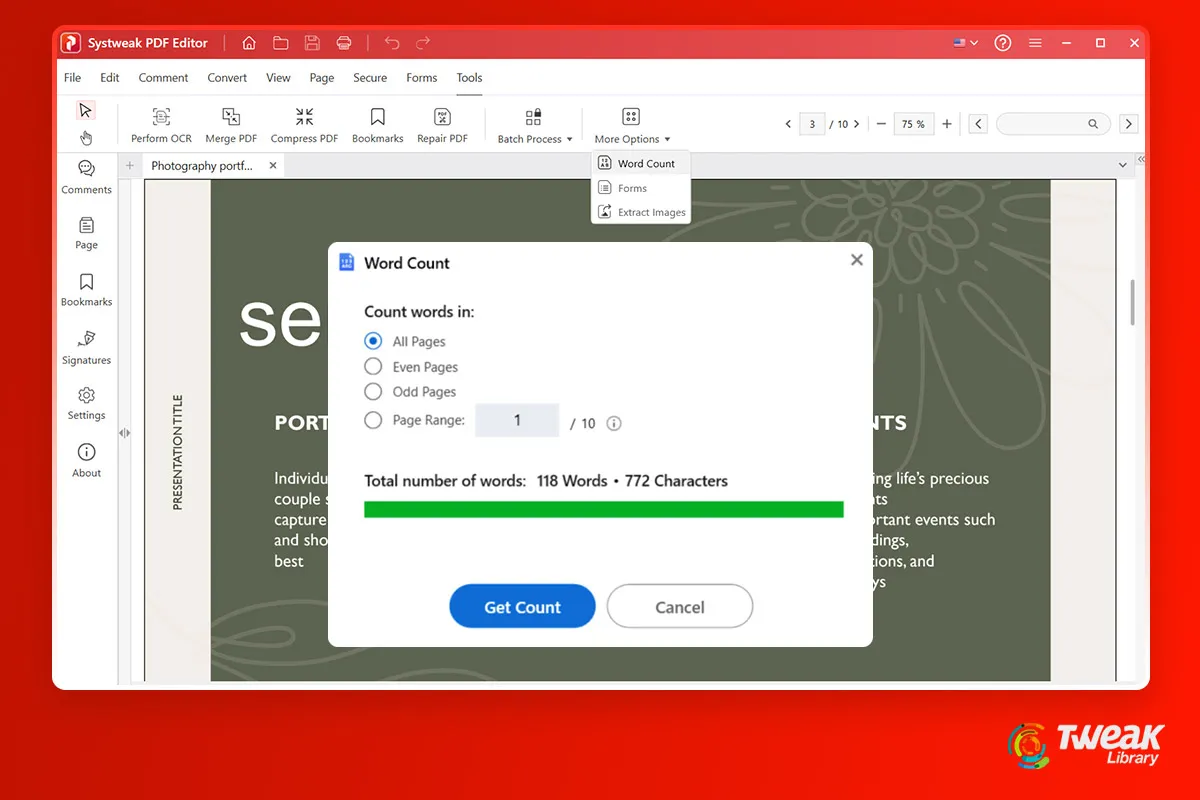
There are instances when you have to limit your words to a certain word count. But, suppose you have converted your document to PDF and then, have to ...
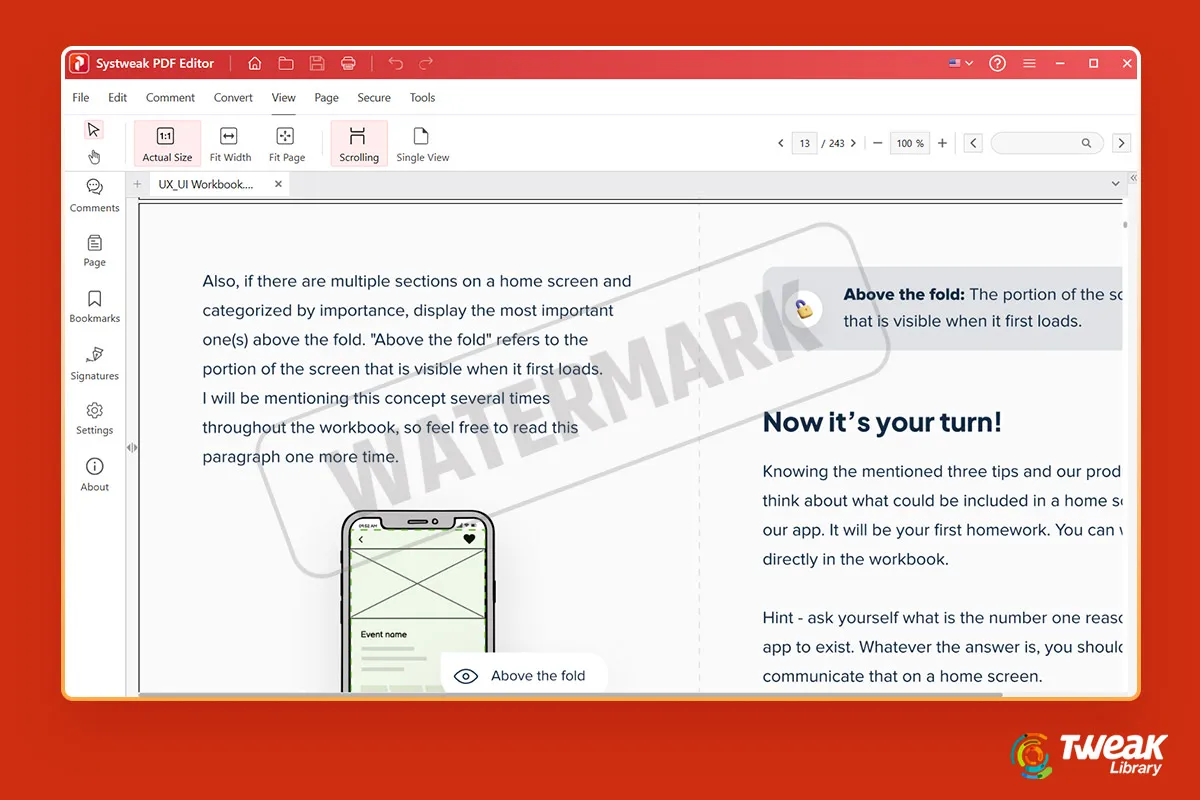
Many of us save our work which is originally in text documents as PDFs. If you are looking for some of the best ways to convert Word to PDF, check out...
HTML or Hypertext Markup Language is a code that defines the structure and content of the web pages of any website. Whether you are a web designer, a ...

On an Apple forum, we came across an issue where a user wasn’t able to pair their Apple Watch to their iPhone - Normally, an Apple Watch pair...

TIFF refers to Tagged Image File Format. It is a file format known for storing raster images and graphics information. It is preferred for its high im...
For various reasons, you might want to save your Excel file as PDF. It could be that you want to save your Excel as a PDF so that other users can’...

The Apple Glowtime event was held on September 9, 2024, at Apple’s headquarters in Cupertino, California, US. The latest iterations of its core prod...
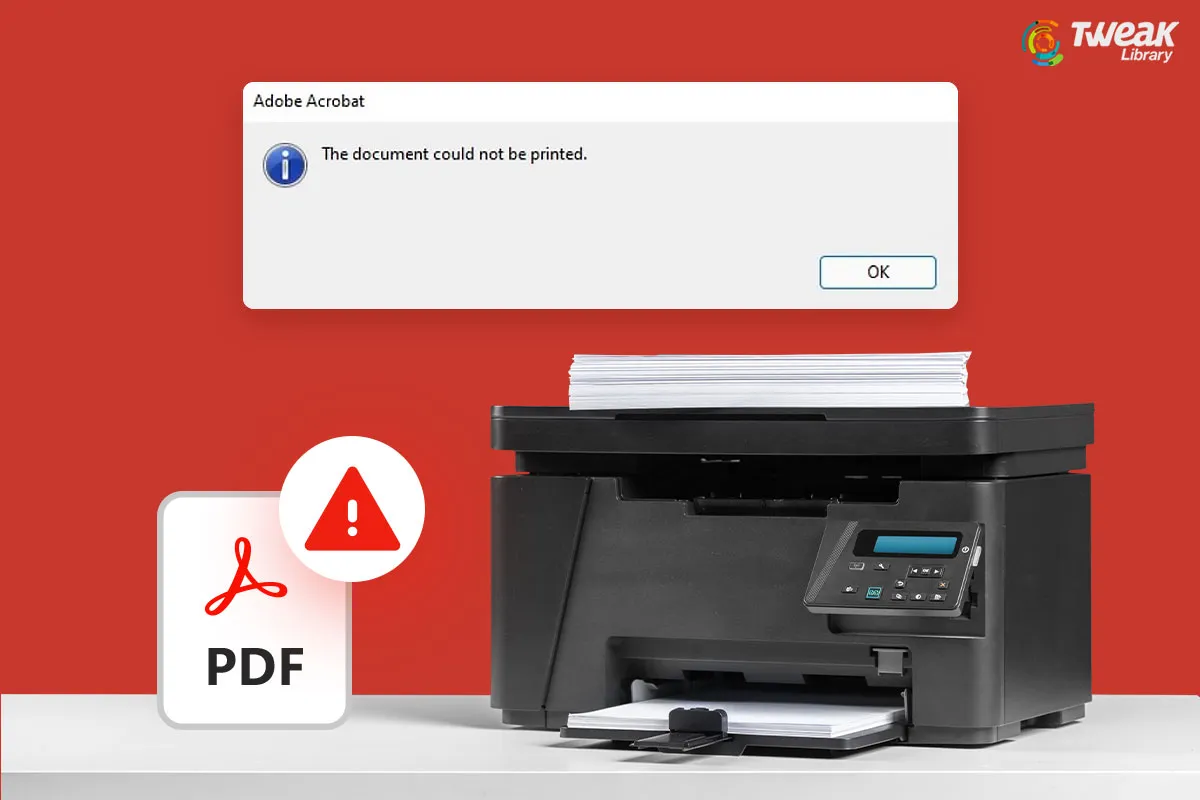
It’s frustrating when you have to print a PDF file for evaluation urgently but you face an issue. There could be several reasons why this issue is s...