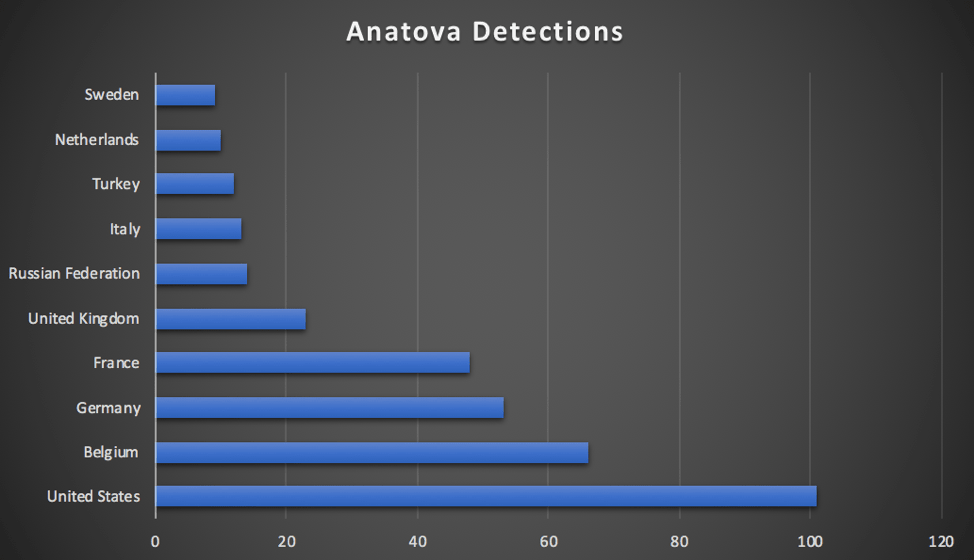
When everyone was busy celebrating the new year, cybercriminals were busy making a new type of ransomware for 2019. This ransomware is considered dangerous as it can be turned into a multifunctional piece of malware by its skilled creators. The ransomware we are referring to first emerged on January 1st, 2019 and is named Anatova based on the name on the ransom note.
So far it has found infecting hundreds of machines around the world. This ransomware disguises as applications, games tricking the user into downloading and installing on the PC. Moreover this, ransomware includes an anti-analysis routine and is referred to as modular ransomware.
Also Read: Future Of Ransomware In 2019 And Beyond
What is modular ransomware?
Although the primary activity of a ransomware is to encrypt data, Anatova cryptoransomware is capable of infecting user’s PC in other ways too.
This ransomware runs on a different algorithm and execution technique. This tells about Anatova’s nature and plans to infect PC’s using modular techniques. Anatova ransomware is coded with advanced technology and is found to be destructive.
Therefore, here we bring for you a detailed analysis and prevention techniques from Anatova ransomware.
How does this ransomware work?
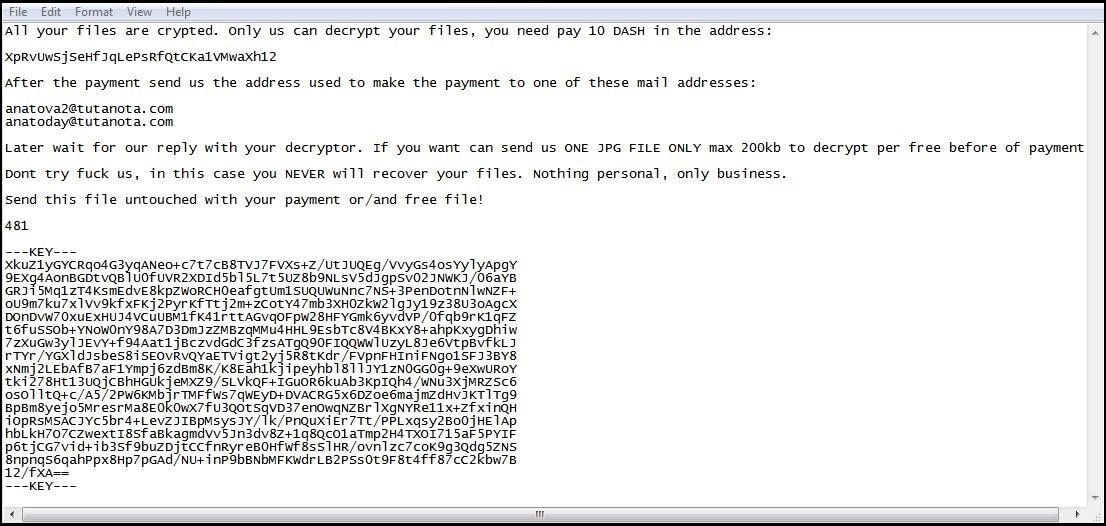
Once installed, Anatova ransomware seeks admin privilege, runs a few checks, encrypts data and demands 10 DASH coins, currently valued at $700.
Moreover, Anatova the cryptoransomware like other ransomware does not add an extension to the encrypted files. Anatova encrypts all files, leaving system folders, it even skips Windows files, desktop.ini, pagefile.sys, .exe. cmd extensions etc.
File skipped by Anatova ransomware during the encryption process
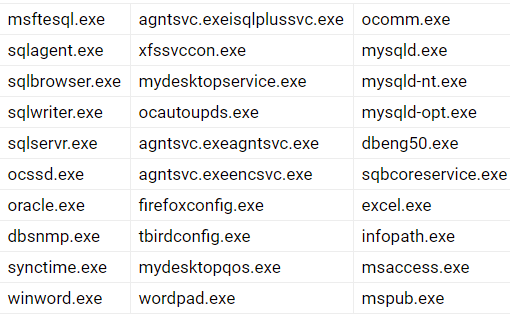
Anatova cryptoransomware encrypts files = < 1MB file size, if the file is greater than 1MB, only 1MB of data is encrypted from that file. As suspected by security researchers Anatova follows this practice to avoid detection by security software.
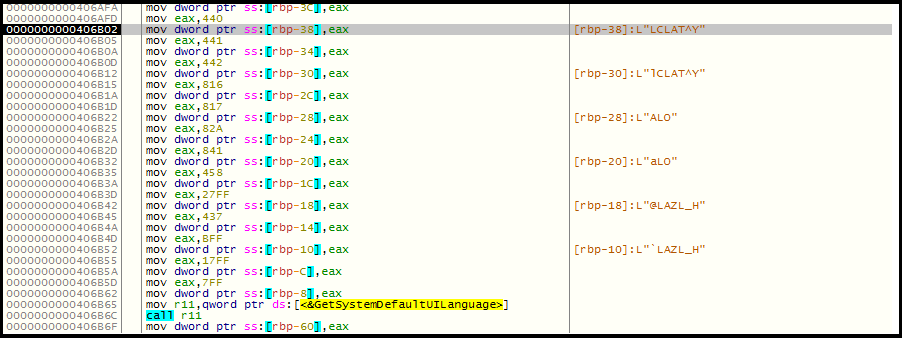
In addition to this, the ransomware uses anti-analysis technique after entering into the system. For this it first gains system information, username by using GetUserName API, it matches username with saved blacklisted username. If the matching username is found, ransomware will move for clearing out and exit the process without performing any activity.
Skipped usernames are as follow:

Further, Anatova ransomware uses GetSystemDefaultUILanguage API to know the system’s language at the time of the first installation. This is done to know whether the activity needs to be performed or should it be skipped. There are few countries where Anatova crypto-ransomware will do no harm.
How Anatova ransomware encrypts data?
Once all checks are done, Anatova starts encrypting data, for this, it uses a combination of RSA and Salsa 20 algorithm. To avoid encrypting same files, Anatova adds a marker of 4 bytes at the end of the file. Further, after encrypting data and removing Windows shadow copies, Anatova ransomware deletes itself and drops a ransom note.
Shaken! after knowing all this?
Don’t be there’s good news. Windows users can use Systweak’s Advanced System Protector to add an additional layer of protection. Mac users can use Systweak Anti-Malware. Both the tools offer auto database updates, thorough analysis and detect all the latest threats to secure your system.
How to stay safe and protected from ransomware attacks:
- Backup your important data on the cloud or an external drive. If you want to take backup on the cloud, try using Right Backup. A reliable cloud storage service.
- Avoid installing and using freeware or cracked version of any product.
- Avoid falling for online ads and opening them. If they look deceiving avoid opening them.
- Disable macros while using MS Office.
- Use updated antivirus to protect and keep your system form latest and unknown threats.
- Avoid clicking on unknown links or downloading attachments received from unwanted or suspicious sources.
By keeping these points in mind one can secure data and system from malware attacks. Certainly, there’s no method that guarantees 100% protection. But by following these tips one can surely stay one step ahead and can secure the system from attacks.
Must Read: All You Need to Know About Robin Hood Ransomware
This is all for now about Anatova ransomware. Once there is more information about this crypto-ransomware we will update you. Stay tuned to know more about it and practices you should follow to stay safe from ransomware, malware and other types of online attacks.



Leave a Reply