Malware targeting Android devices like Joker malware, MobSTSPY have become very common. In this respect, a new malware strain called TangleBoat is out in the wild. The malware, through unsuspecting means, is planted in the user’s device to steal data and record activities.
First surfaced in September, the Android malware targeted users by sending fake information about COVID-19 vaccination appointments.
Recently, the same malware was detected, sending false information about local power outages. TangleBot uses SMS to trick people into clicking on malicious links. However, the content used in the message is different.

TangelBot is taking advantage of the biggest fear Pandemic (COVID-19 vaccination appointment). However, this practice is disgusting but is effective.
How does TangelBot Malware Work?
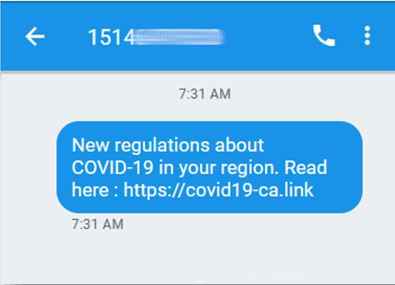
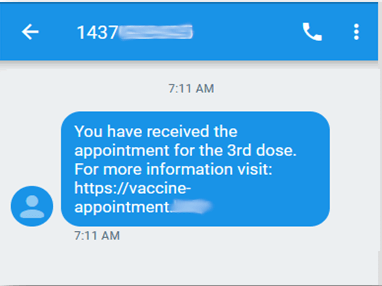
Targeting Android users in the U.S. and Canada, TangleBot malware is distributed via phishing SMS containing information about COVID-19 vaccination or a potential power outage. To take advantage of users, attackers place a malicious URL within the text message, which, when clicked, takes the user to sources from where malware is installed.
Unsuspecting what’s happening in the background, the malware is installed when presented with different boxes seeking the user’s permission to install from unknown sources.

How Dangerous is the New Android Malware?
Once the Android malware TangleBot is installed on the phone, it gains access to the device’s contact text messages, GPS microphone, and other connected applications. This Android malware is capable of performing the following activities.
- Make unblock phone calls.
- To hide legitimate apps uses overlay screens.
- The new Android malware is capable of recording the camera microphone audio and even the screen. All this is directly streamed to the attacker.
- Send, receive and process text messages.
- Observe activities performed on the Android device.
- This new Android malware can steal your account details, and it is way more effective than the other similar Android malware detected.
How to Stay Protected from Android Malware Attacks?
To stay protected from Android malware, security researcher suggests following these security practices:
1. Carefully read the SMS warning before clicking any link received in the text message.
2. Keep yourself updated about the suspicious text messages floated across by cybercriminals.
3. Before sharing your phone number with commercial entities or other enterprises, make sure they’re genuine.
4. If you receive a text message containing a link about package delivery notification or about go with 19 vaccination, avoid clicking on those links directly or use your device browser to access the direct website of the vendor.
5. Avoid replying to unsolicited or messages received from an unknown person.
6. Do not install software available to load outside the certified app store.
7. Before granting any permissions, read them carefully. If you think an application does not require them, avoid granting access permission.
8. It is your right to stop an application if it asks for permissions you are suspicious about.
9. Use an antivirus on your Android device; this will help you stay protected against any sort of threats. for this, you can try using Smart Phone Cleaner , an amazing and free to use malware utility for Android users that scans your Android device and keeps it secure from any sort of threads
Next Read – Free Android Malware Removal Apps
How to Use Smart Phone Cleaner (Recommended Solution)
Use Smart Phone Cleaner, the best mobile cleaner, and security app to optimize and protect your smartphone from existing and upcoming threats and vulnerabilities. Simply run a comprehensive scan using Smart Phone Cleaner to get rid of potential virus and malware infections.
Please follow the steps provided below to learn how to use Smart Phone Cleaner:
STEP 1 = Install Smart Phone Cleaner on your device from the official Google Play Store.
Click Here To Install Smart Phone Cleaner
STEP 2 = Launch the Android cleaning and security application on your Android device.
STEP 3 = Navigate to the Malware Protection module and initiate a scan to detect harmful threats.
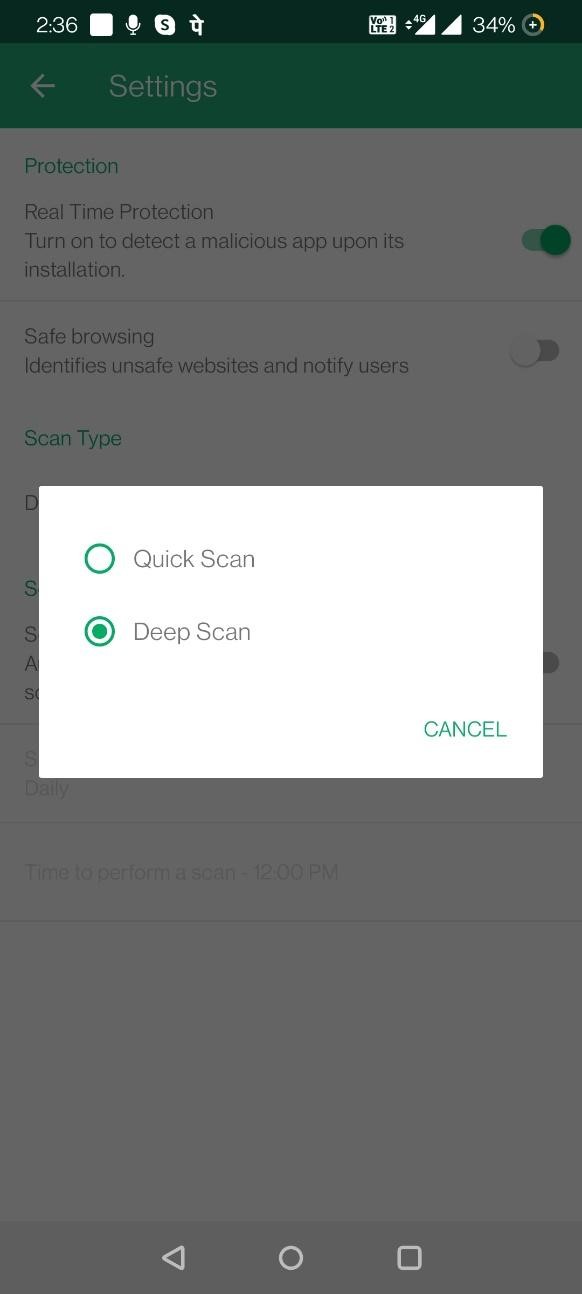
STEP 4 = By default Smart Phone Cleaner runs a Deep Scan. If you wish to change it, go to the Settings, under Scan Type, simply select Quick Scan and you’re all set!
STEP 5 = Wait for the scanning process to get completed. Review the scan results and fix all the detected threats.
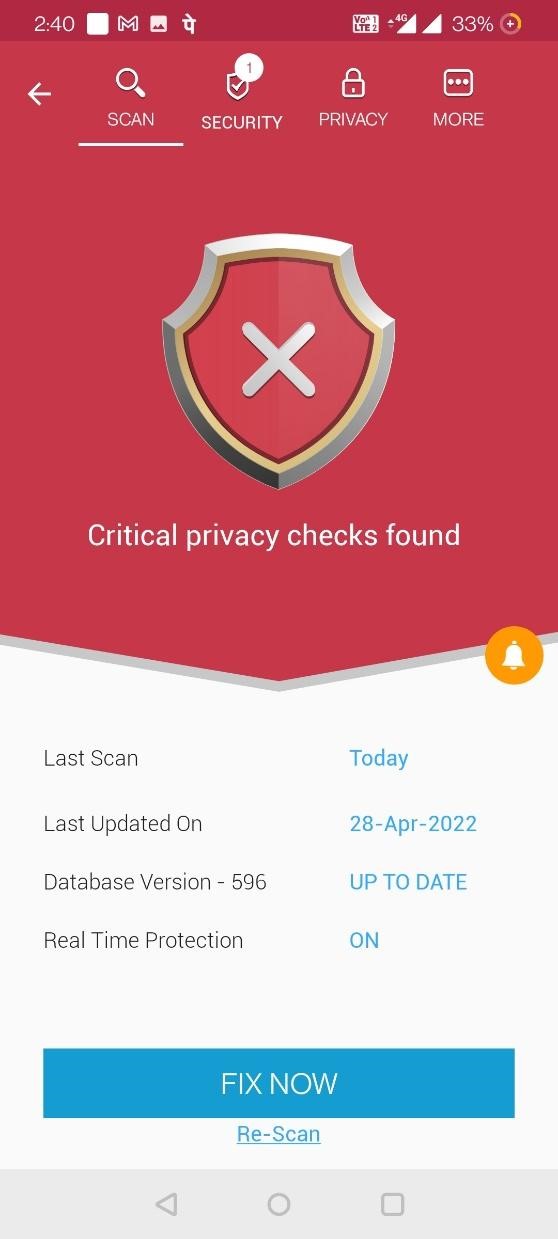
In addition to this, using the multiple cleaning and optimization modules, you can enjoy a significant performance boost in a couple of taps. Smart Phone Cleaner comes with a junk cleaner, duplicate finder, file explorer, game speedup, app manager, and more. You can even run automatic scanning using the in-built scheduler to keep a check on your device’s privacy and security.
To know more about Smart Phone Cleaner, you can read this post: How A Cleaner App for Android Works?
Conclusion
That’s all; by keeping these security tips in mind, you can stay secure from malware attacks targeting your Android devices.
Though TangleBoat is currently targeting North American users, it doesn’t mean you are secure.
To stay protected, you need to be careful about the online activities you perform. TangleBoat malware steals banking information, the most looked upon data on the dark market.
The only way to stay safe against these attacks is to be very careful about the users’ activities and actions. We hope you found that article interesting and it has added some value to your knowledge. We look forward to hearing from you regarding the same.







Leave a Reply