We all have indulged in content piracy and have tried to get our hands on our favorite entertainment content by illicit means, avoiding both subscription charges and geological restrictions placed on the streaming service companies. Though this has allowed us as users to not miss any of our favorite films, shows, and live matches; however, we are simultaneously risking our identity and our network safety. Read ahead to know why our torrenting ways may not be suitable for our own selves.
Piracy of Video Streaming Sites and Applications

Entertainment services have become the most successful business industry internationally by utilizing internet and cloud computing to provide real-time entertainment content to users. Entertainment companies have turned to internet streaming of video content allowing enthusiasts of film, television, and sports to watch their favorite and desired content relaxing at home. Since the amount of data of such content available on these streaming platforms outmatch of that available in DVD formats, these sites and applications have become the first choice of every user across the globe.

But, these services come with a heavy annual or monthly subscription charges. Which actually gets high every year or two. Moreover, these charges change country to country and may not fall into the budget of every user. Other than that, the content available on these sites varies from location to location, thus, refraining people from accessing international content.
But people being people, tend to have it all without even paying for anything and resort to improper and unauthorized means to access these services.
How Users Carry Out Piracy?

Earlier, torrenting was the most common medium of getting video content in regard to film, television, sports, and even music. People used to download this content instead of buying it on DVD via portals like BitTorrent. This was done because the internet services everywhere were not as efficient as the present day and did not support high-quality streaming of content.

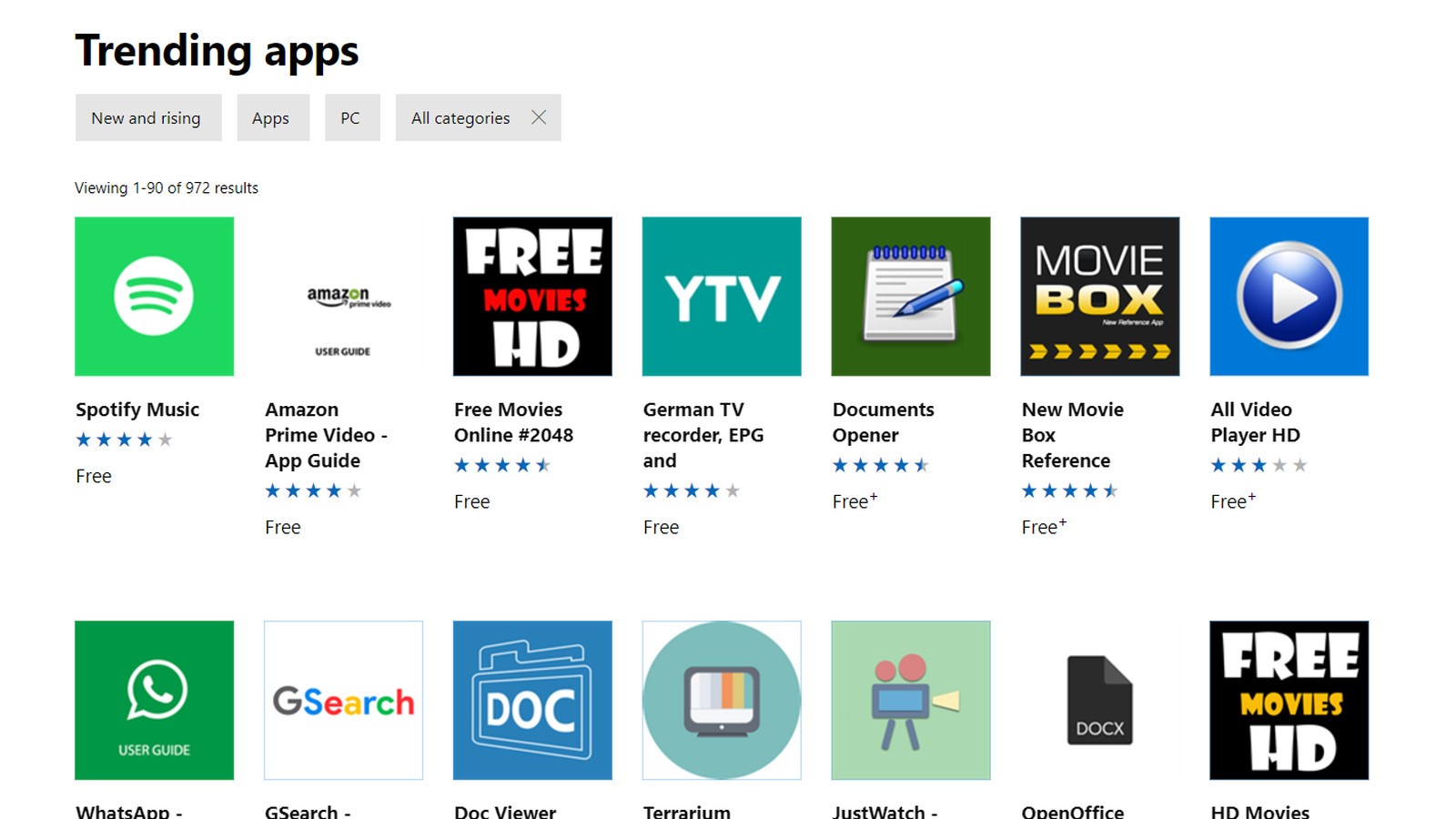
But since the internet has become more flexible and has reached to almost every geographical location, illicit developers have resorted to designing applications resembling that of the prominent streaming services like Netflix, which they are spreading across the web, allowing people to download them. Commonly known as “hack-apps”, these apps offer the same content as their original counterparts but for free. The “free” part is what attracts users the most.
But, unknowingly they all agree to terms and conditions without reading them on these hack-apps and jeopardize their safety and internet security.
Also Read: 10 Best Free Video Calling Apps for Android
Hackers Threatening Your Identity and Network Security via Such Apps

Just like original entertainment sites and streaming applications, these hack-apps require registration via your ID and ask you to agree to their privacy and user agreement terms. Those terms which we never read. However, the developers of these hack-apps do not guarantee your data protection and they never agree to not use your information or preferences you make while using their app. They may use your email address and procure whatever information they can get using the ID. In case the similar email address is associated with other services you use, the hackers can easily gather that just by having your email address.
This makes you highly prone to identity theft and information abuse, which may further subject you to financial frauds as well.
Hackers Go Next-Level With Pirated Streaming Sites and Applications

In a recent incident, a pirated streaming service application called Mobdro (see image above) was found to be injected with malware which can hack into your network by stealing your Wifi credentials and passwords. Mobdro is an illegal application that allows users to watch entertainment and sports content. In case your network is breached you can be subjected to numerous malicious activities, along with hijacking of other files and accounts that are uploaded on your network. These are a few instances that can occur if you fall prey to a malware-infected application like Mobdro:
- Such malware has high chances to go undetected. Most of such malware would store your stolen credentials and password to your network connection in an overseas server. So, good luck catching your attacker.

- Once your network is breached, hackers can get into any device that would connect to the same network and can carry out account hijacking or phishing attacks on those devices as well.
- Your network credentials would allow hackers to upload more malicious files on your system and make it more vulnerable to cyber-attacks.

- These applications, once into your used network may also hijack other applications stored on your device and jeopardize their reliability as well.
- Hackers can upload rootkit malware in your system via hacking into your network, which would give them unauthorized control of your device and would enable them to further scrutinize your files and folders.
Must Read: How To Spot Fake Videos On The Internet

- Though it’s highly unlikely to happen to an individual user, network breach can also make your system vulnerable to ransomware attacks.
Is There A Solution To This Problem?
These apps are willingly used by people to fulfill their interests and it’s up to them to avoid its harmful impacts on their network and internet security. It is advised to not use such applications and always go for the authentic versions of video content streaming services. Though the authentic versions of these sites and applications come with a number of restrictions and may be unaffordable charges. Given the guaranteed security of your network and encryption of your preferences and data, that subscription amount is worth paying for.






Leave a Reply