Malware developers generally write programs for technologies that are widely used. They have always practiced methods on bigger scale to attract more victims. They design traps that ask users to open emails and access attachments. Malware terminology has evolved from basic Trojans, virus and spywares to Crimeware, krugueware and so on.
The main concept of antimalware program is to protect a system by catching malwares with signature database: – they block only what they know. However, the experts in safety estimate that the authors of malwares constantly accentuate their efforts to encrust themselves in the mobile peripherals. Threats and Malwares are becoming more and more sophisticated.
Another worrying trend is that many of these spy malwares also include multiple destructive capabilities. Installing and updating antivirus software that monitors communications and prevents unauthorized programs from being run remains the best form of protection against malwares.
Also Read : Black Rose Lucy – A New Malware-as-a-Service (MaaS)
The limits of signature database file protection are evident: -any programmer can create his own malware for his own goal: the less his tool is noisy, the more he has chance of success. Since a malware is not discovered in the wild, and reported or submitted, it can still unknown for a long time. -Antivirus is mostly designed to combat malwares, and not attacks. -even the most exhaustive malwares databases (Webroot, Kaspersky and so on) can’t take the census of ALL available malwares. Current known Mac OS X malware count is very less, which makes it so pretty much non-existent at the moment. However, with Microsoft Windows operating system being dominant in the desktop market, it is clear why most malware is designed for it.
Also, prior to Vista, the various Windows versions were pretty much wide open, full access, making it relatively easy for malware to abuse. If you use a webcam for online chatting, your computer may be at risk from a new strain of computer malware that gives hackers control of your webcam, enabling them to turn it on, capture video and send it back across the Internet. Mark Sinclair, Trend Micro technical services manager says, Malwares that allow hackers to peep through webcams are stealthy programs not easily detected by the average user. Besides, some malwares disable the sound card so that no sound will be heard when the camera is turned on.
If a notebook with an internal webcam is infected with one of these malwares, someone may be spying on you the next time you turn on your computer. In addition to malwares that take control of webcams, security firms like TrendLabs has also detected malwares that take screen shots of whatever programs are running on a computer. Another worrying trend is that many of these spy malwares also include multiple destructive capabilities. Installing and updating antivirus software, which monitors communications and prevents unauthorized programs from being run remains the best form of protection against malwares. We recommend you Advanced System Protector for Windows. It is a sophisticated antimalware software that is designed to kill different types malware namely spyware, trojan, password stealers, monitoring programs, PUPs, key loggers, riskware, heuristics and many more.
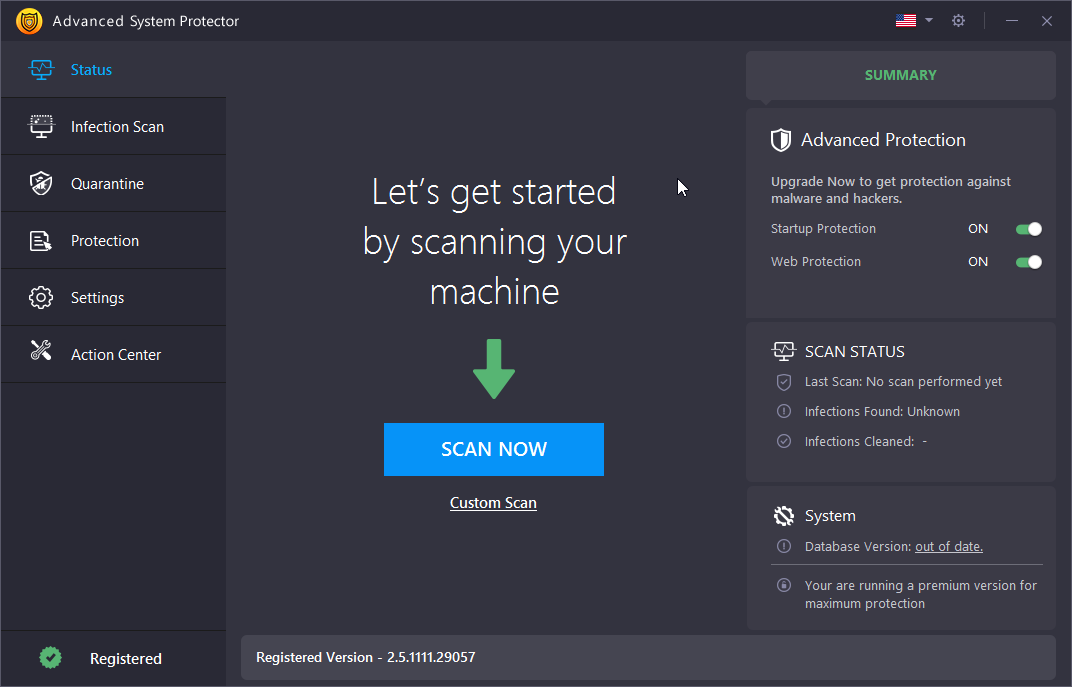
Advanced System Protector contains three modes of scan i.e. deep scan for thorough scanning of your entire hard drive, custom scan for scanning requisite folders and files and quick scan to scan your computer at faster. Its database consists of different malware definitions that gets constantly updated by the security experts at Systweak. Click on the button to download the software.







Leave a Reply