An uncommon Linux cryptocurrency miner known as LoudMiner, is being distributed for macOS and Windows since August 2018. This cryptocurrency malware is using a clever cryptojacking technique to mine Monero.
LoudMiner uses virtualization software QEMU (Quick Emulator) on macOS and VirtualBox on Windows to mine Monero on a Tiny Core Linux virtual machine. It is pushed through pirated copies of Virtual Studio Technology (VST) like Propellerhead, Nexus, AutoTune, and others.
VST is an audio plug-in software interface that mixes software synthesizers and effects in digital audio workstations. Compromised machines are used to mine cryptocurrency and uses SCP (Secure File Copy) with embedded username and private SSH key to self-update.
Loud Miner malware targets audio applications that have high CPU usage making it difficult for the user to identify unusual CPU behavior.
How is LoudMiner Distributed?
At the time of writing LoudMiner is distributed via a single WordPress based website linked to 137 VST out of which 42 are for Windows and 95 are for macOS. However, instead of being hosted on WordPress based site they were hosted on 29 external servers that can be found on IoCs section.
What makes LoudMiner so clever and uncommon cyrptojacking malware?
Size of the app is what makes it impractical to analyze them. Also, site admins frequently update applications making it difficult to track the first version of the miner. Moreover, LoudMiner cryptojacking malware seems to target machines with high computing power, making detection difficult and mining cryptocurrency easy.
In addition to this, malware developers don’t need to compress Tiny Core Linux virtual machine and coinminer as VST hosts are quite large. Making victims install LoudMinder willingly as the pirated VST software comes bundled with virtualization software.
Also Read: How MacOS Deal With Malware
How LoudMiner infects Windows and macOS?
On Windows machine, LoudMiner uses a batch script to launch coinminer’s Linux image to make it run at each startup. While on macOS, LoudMiner adds “plist files in /Library/LaunchDaemons with RunAtLoad set to true” ensuring nasty process keeps running.
How to stay safe from LoudMiner attack?
Staying safe from malware attacks is not impossible. By following certain points in mind, you can easily protect yourself from LoudMiner attack:
- Avoid downloading pirated copies of commercial software.
- Keep an eye on popups from unknown installers, higher CPU usage.
- Beware of new service and connections.
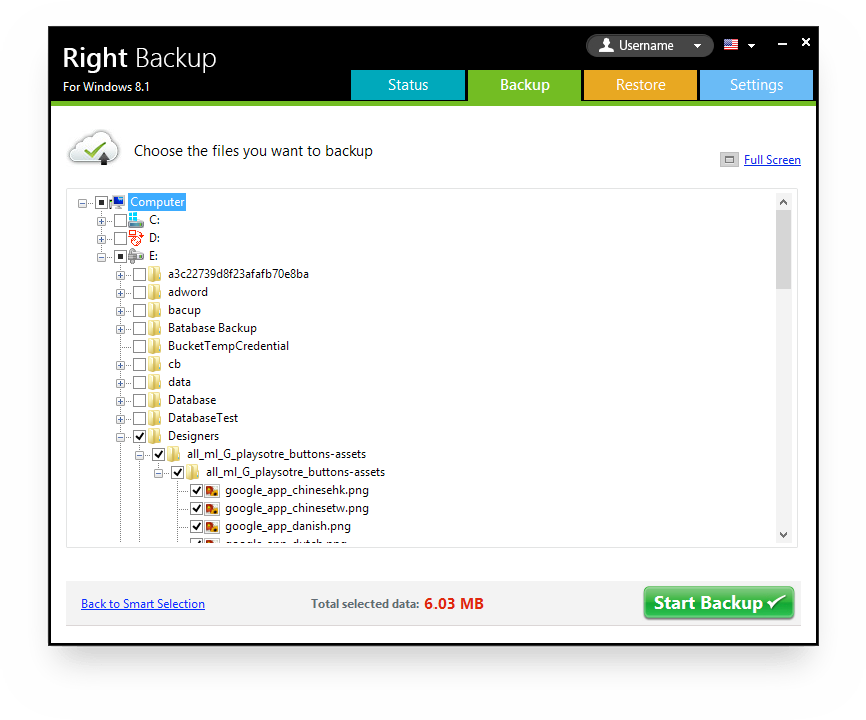
Using these simple steps and by avoiding downloading pirated copies of the software you can stay safe from LoudMiner and similar threats. Along with it, you should always keep your data backed up. For this, you can try using Right Backup – a cloud backup tool.
Certainly, the technique LoudMiner uses depicts how clever attackers are and our mistake can make us a victim. With this, we hope you stay safe from attacks. If you like the information do comment and stay tuned to keep reading about the latest threats.






Leave a Reply