
The problem “You need to format the disk before you can use it” arises when you are trying to access any kind of hard drive on your computer. It c...
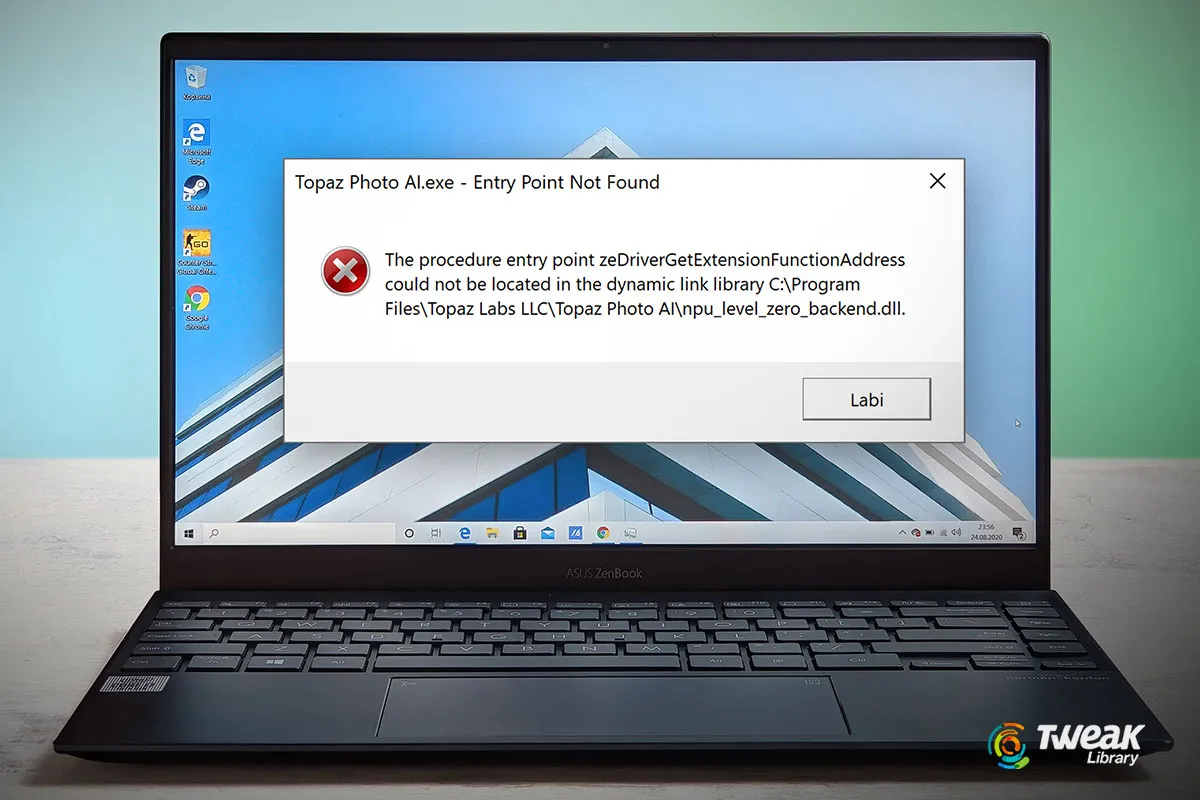
Have you ever run into an issue when your commonly used software suddenly stopped working and returned the “The Procedure entry point could not be l...
Whether in an office or personal usage, emails have become an important part of communication. Outlook is one email client that lets you manage emai...

There is no doubt that Microsoft Word is one of the best word processors and has been around for years. But, you may want to switch it up with a subst...
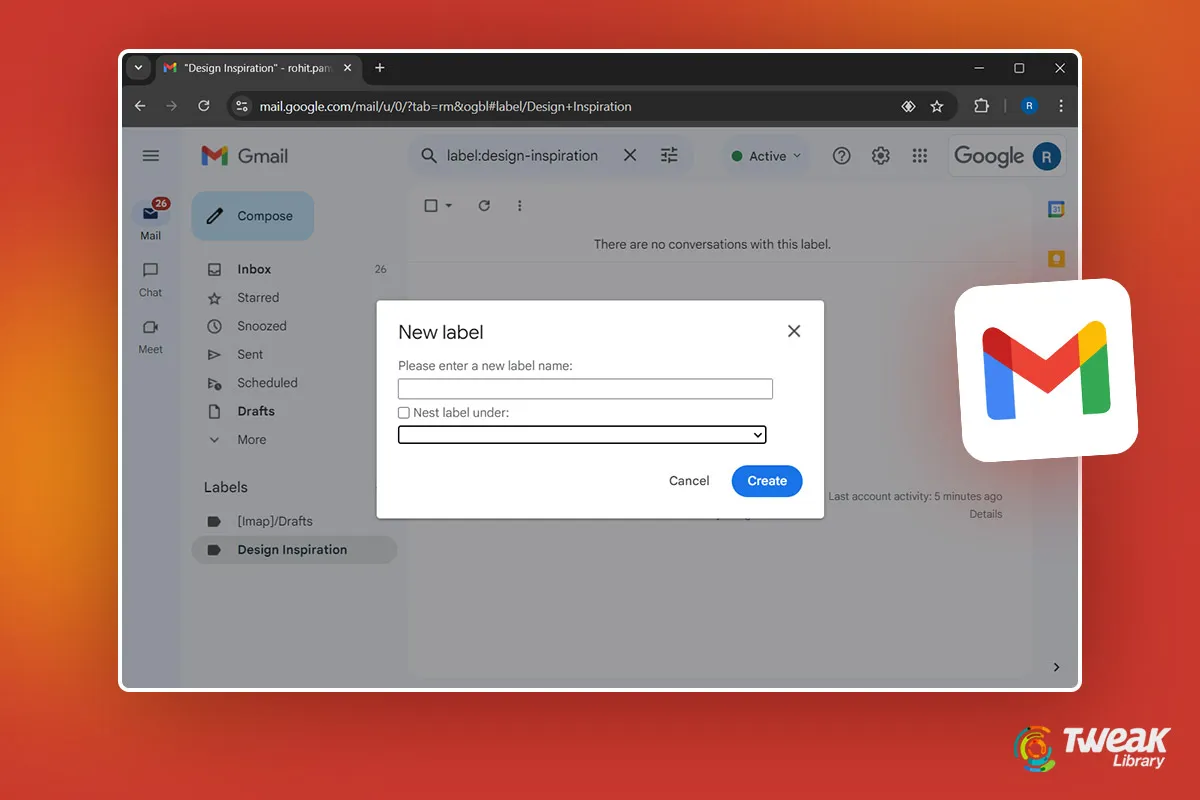
When you have thousands of emails flooding your Gmail, it would be better to organize them into categories. Well! Gmail lets you create labels with wh...

It’s a painful sight when despite entering your login credentials correctly, you have to wait for an eternity to log in to your computer. To put thi...
PowerPoint slides are a great way to showcase information with graphics, animations, transitions, and other effects. Indeed, they are a great way to c...

Do you often FaceTime your friends and family? If yes, did you know, you can save live photos while Face Timing your loved ones? If not, here is how y...

A powerful and feature-rich screen recording app can help you capture the on-screen activities of your Android smartphone with precision. Speaking ...

If you have paired your Apple Watch with your iPhone, you can make and receive calls and send and receive messages without your iPhone. Shocked? All s...

There are times when working with multiple PDF files, you also have to be wary of the number of pages in the PDF files. This helps you stay within pag...
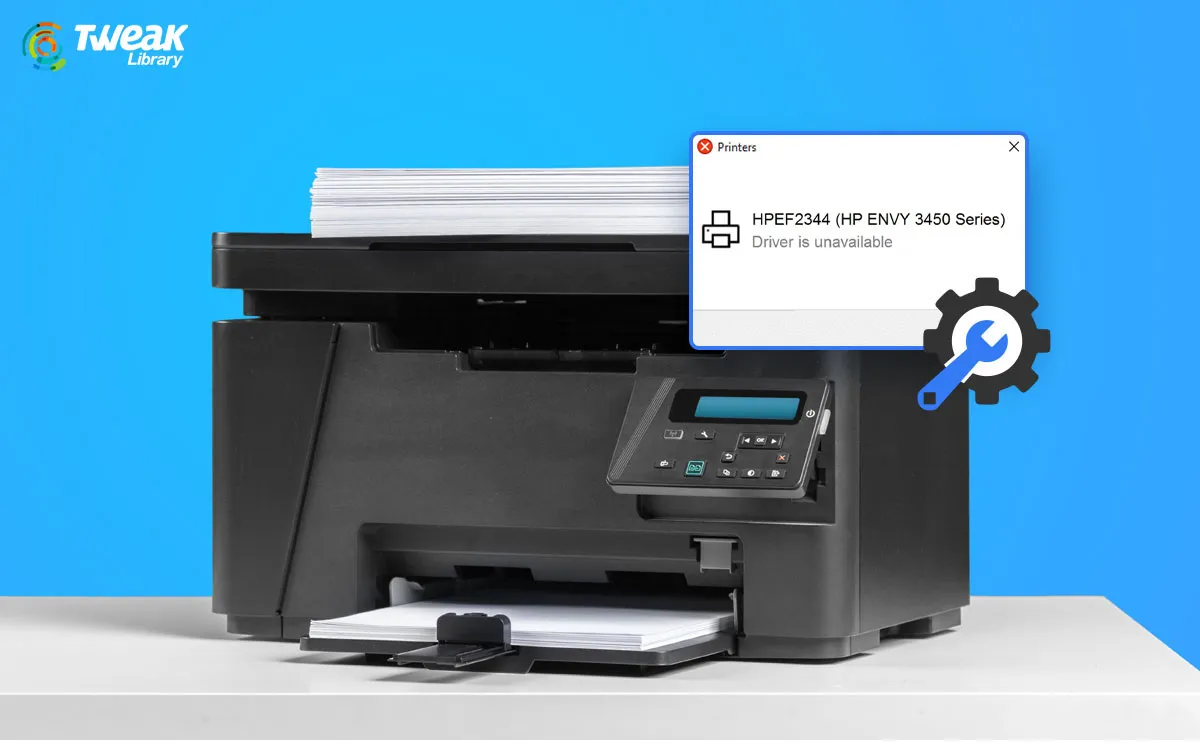
Printing documents using a printer should be a hassle-free process. However, there are times when you may not be able to print documents smoothly beca...