Malware is a type of program which is used to perform malicious activity. Malware is a combination of two words Malicious and Software. It is short form of malicious software.
In this article, we will discuss about Malware and its types. There are lots of malicious programs available on the dark web. All the malware work entirely different from each other.
Malware in Simple Language
Malware stands for malicious software, this software is used to steal important information, gain admin controls, cause harm and disrupt normal working of device.
Virus

A virus is a type of malicious program that replicates itself on a system. It modifies all the files in a system and then changes them into itself. They spread onto different computers by infecting the file, and when that file is executed on another system it affects whole computer.
There are different functions that a virus can perform like stealing information, harm system and networks, create other malicious programs, and more.
Also Read: Life Threatening Malware: Triton
Adware:

It is also known as advertising-supported software. This type of malware will automatically show ads on user’s system. By showing ads, it will generate revenue. It will generate revenue by displaying ads on the system and by pay-per-click basis.
Users get bombarded with the advertisements on their system, in which there are different types of advertisements.
Sometimes Adware is designed to steal user’s information and track their activity making it dangerous.
Bot

Bot is a type of malware which are designed to perform specific tasks. It runs automated commands. This malware is used for DDoS, stealing of information, sending spam messages, and it also allows attacker to access device and its connections.
Bots affect PCs, mobile devices, IOT devices and even whole networks. Infected devices will work as a group to perform biggest tasks.
Ransomware
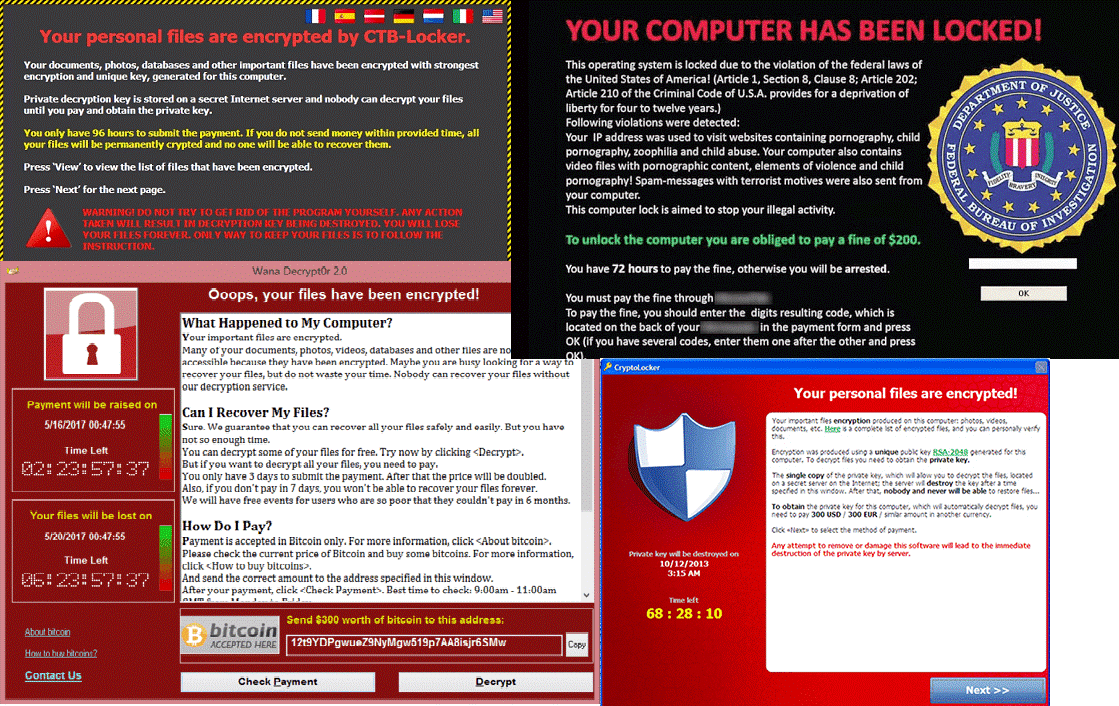
Ransomware is a kind of malware which locks all the files on the system and then demands ransom to unlock it.
User’s usually get the warning on their system that their files are locked and to unlock it user must pay requested amount. Usually this amount must be paid in form of Bitcoin.
Ransomware can get into system by different ways. It can get into your system by phishing mails, infected software, and other online sources.
Also Read: Five Important Functions required In An Antivirus Software for MAC
Rootkit

Rootkit is a malware which grants admin rights to the attacker for victim’s computer or network. It hides itself and works without being detected.
Once it is installed on the victim’s system it remotely accesses sensitive information stored on victim’s system.
Rootkit can be used to install other types of malwares which will then be used for other attacks.
Rootkits are hard to detect as they are hidden in the system, many security products are unable to detect Rootkit and generally bypass them. To detect Rootkit, you have to be self-aware and continuously monitor their network activity.
Spyware:

Spyware is a type of malware which spies on user’s activity without their knowledge and steals their information. Spying activity includes collecting keystrokes, accounting data, and collecting personal information. These types of malware have many capabilities like changing security and system settings.
Trojan Horse

Trojan horse is also known as Trojan. It is a type of malware that tricks user into installing itself disguising as legitimate software or file.
When a user installs or runs malicious file, this malware starts its malicious activity. Once the system is infected this malware starts sending user’s information to attacker. This malware also gives remote access to the hackers.
Trojan can be used to infect victim’s system with other types of malware also.
Also Read: Keyloggers: How To Stay Protected?
Worm

These are the basic types of malware and the most common. These types of malware generally infect the system exploiting OS vulnerabilities. Typically worms consume bandwidth and overload web servers. Worms often contain piece of code that affect host computer. These codes have different functionality, they are designed to steal data, delete them, or create other malware.
Worms are considered as virus; however, they are completely different from them. They do not replicate like virus, worms spread through human activity. When user runs an infected file, download infected file or installs infected software, worms get into the victim’s system.
How to Check If Your System is Infected?
Different malware have different behavior but their symptoms are somewhat similar.
We have listed some of the symptoms below:
- Increased CPU usage.
- Slow working of whole computer and software.
- Network issues.
- Crashing and freezing of the system.
- Deletion of files and modification of files.
- Unwanted file creation.
- Unwanted installation of the software.
- Creation of unwanted desktop icons.
- Disabling of security software.
- Reconfiguration of antivirus and firewall.
- Unwanted sending and receiving of emails.
Removal and Prevention of Malware
There are different methods that users can use to get rid of malware. Different types of malware need different treatment methods. However, we have listed some common methods that will greatly increase your system’s protection.
Removal
If your system is infected with malware you can take these steps below to get rid of it.
Immediately shut down your system: If your system is infected, do not perform any action on your system, just shutdown it.
Start your system in safe mode: After shutting down your system, start your computer in safe mode. In safe mode, many services of the system are disabled and it can prevent your system from further damage.
Install good security software: Install and run good antimalware software on your system.
You can use Advanced System Protector for Windows based system.
For MAC based operating system you can use Systweak Antimalware.
After ensuring that your system is safe, start your system in normal mode.
Prevention
It is always said that prevention is better than cure. We should always be ready for malware attack.
We have listed some points using which you can prevent malware attacks.
- Keep your system always updated: OS manufacturers always release updates which contain different patches, which prevent from different new malware.
- Keep check on software downloads: Before downloading any software, always make sure that you are downloading it from a legitimate source and it may contain malicious software.
- Keep all your software updated: Always make sure that you have good security software and it is up to date as every day new virus definitions are being released by companies.
- Always make sure to use popup and ad blocker: Always make sure that you are using popup and ad blocker. This software will prevent any unsolicited advertisement coming to your system when browsing the Internet.
- Firewall: Do not forget to use Firewall. Firewall is the main line of defense of your system. It will block and notify users about any incoming and outgoing Internet connection.
- Visit secure websites: Always visit secure websites, you will see https written instead of http in the address bar. Visit only those websites on which you have full trust. Also, before entering any information on any website make sure you are on the right URL.
Also Read: Safeguard Yourself on Public Wi-Fi Hotspot
Conclusion
Attackers are getting better and better with time, they are using different technology and tricks to attack. We have to be self-aware and keep our systems secure. In today’s world, all our information is stored online, which can be accessed by anyone having the knowledge. Thus, it is vital to stay up to date about cybercrimes and how they can be prevented.



Leave a Reply