Amidst increasing cyber-attacks, warnings have been delivered by authorities of Northern Ireland to the staff members.
Every day the world continues to suffer at the hands of hacks and attacks, and yet these types of attacks are being overlooked that lead to multiple system failure and important data loss.
In a recent activity like this, Northern Ireland Assembly issued a warning to it’s employees regarding future attacks. The Assembly has requested staff members to change the password of their systems before any malicious attack happens.
According to reports, an outside source has already attempted to access employees’ emails and systems multiple times using several passwords. The email has been sent to the staff regarding the issue. Acting on it, Information Technology (IT) department of Northern Ireland and staff members have started taking measures against the attempt. They are currently working with Microsoft and National Cyber Security to look out for the solution about the issue.
Also Read : All You Need To Know About SOAPA
In an interview with the local publication, one of the member of the Assembly said,
“The Assembly Commission’s IT system has been subjected to unauthorized attempts to access email accounts. We are taking all necessary steps to manage and mitigate this and are working with the appropriate authorities, both locally and nationally. The Assembly takes the security of its IT systems very seriously and strives continually to ensure that all systems are secure. The Commission does not wish to comment any further at this stage.”
Similar attempt took place less than a year ago on the Houses of Parliament. On this the CEO of Egress, leading provider of privacy and risk management services, Tony Pepper said,
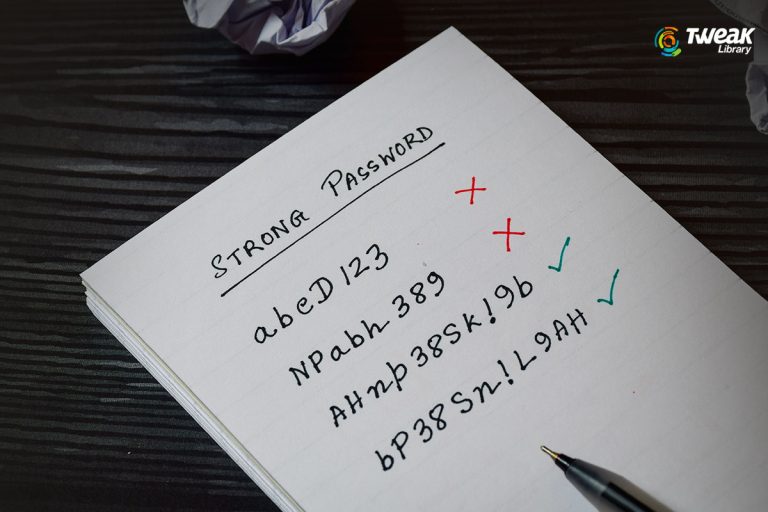
“Both attacks have targeted email systems, trying to take advantage of staffs’ weak passwords to gain access to sensitive information contained in mailboxes. Cyber-criminals come back to this type of attack time and time again because human error is always the greatest area of weakness when it comes to cyber-security”.
Adding on to the statement he also said, “In this attack, and countless others, hackers were banking on poor security practices to help them through the door, such as weak or re-used passwords, and urging staff to update their credentials is simply not enough.”
Now, before overlooking this issue the companies are required to update their security systems to lessen the harm of the attacks and hacks to be occurring in near future.
Pepper also said that, “Should hackers find a weakness, organizations need to be confident that they can’t access the sensitive information that is shared via, and therefore stored in, email systems”.
While addressing the same issue, senior director at One Identity, Bill Evans stated,
“They were inspecting the systems and alerting users to the attack. But again, an ounce of prevention is worth a pound of cure. End user education may have limited some of the risk. One of the first things users need to learn is the use of strong passwords and the risks of weak passwords. Asking users to change from weak to strong passwords after an attack is like locking the barn door after the horses have been stolen”.
In an add on about the attempt he also said, “For example, encryption that secures email content at rest is one way to protect critical assets should the worst happen and a hacker gain access. Good security should work with staff, accepting their behavior will be unpredictable and helping them to be productive while making sure they are not letting cyber-criminals access sensitive content, and in this case potentially putting the public at risk”.
After such an incident, organizations are directed to take the preventive measures as soon as possible to stop such attempts. They should use multi-level authentication and encryption method to encrypt data and save data breach. They should also guarantee the access of the data to limited people so that, only the right person at the right time has access to it and no other breach would be possible after the preventions are taken by the respective organizations.
Must Read : Some Common and Popular Types of Android Mobile Malware
If you found this helpful, please let us know. Give us your feedback in the comments box below.




Leave a Reply