Has your PC been a victim of the havoc that struck the globe recently? Has WannaCry infected your computer? Chances are that you might be lucky and may get your files unlocked without filling the pockets of cyber criminals.
The private cybersecurity industry has already been a victim of some rampant worldwide crises in 2017, including malware attacks such as WannaCry and EternalHacks. However, some counter hacking organizations are trying to save us from the unprecedented destruction and have created a decryptor for WannaCry.
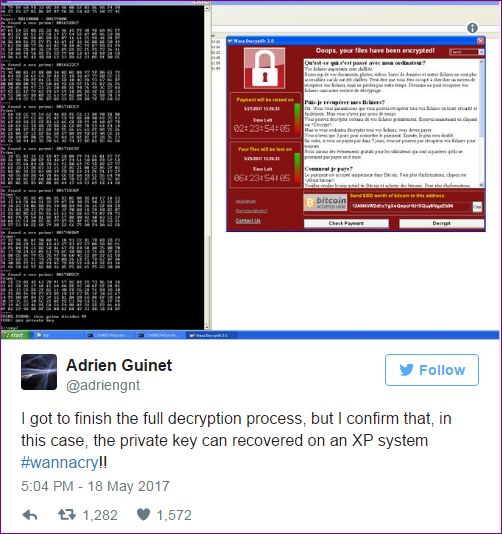
French security researcher Adrien Guinet, from Quarkslab claims to have found loopholes in how WannaCry works. He has finally figured out a way to find out the decryption keys for WannaCry ransomware. The decryption tool is available for free and is said to work on Windows XP, Windows 7, Windows Vista, Windows Server 2003 and 2008 operating systems.
WannaKey: WannaCry Ransomware Decryption Keys
WannaCry ransomware works by creating keys that rely on prime numbers. These encryption and decryption keys are known as “public” and “private” keys and are responsible for the encryption and decryption of files.
WannaCry plays smartly and erases the private key leaving no choice for the victims to decrypt the files on their own. Sadly, they are left with no option other than paying ransoms to the hackers.
Here’s the Loophole: WannaCry though deletes the private key, it did leave a loophole. Per Guinet, WannaCry “does not erase the prime numbers from the memory before freeing the associated memory,”.
Based on this study, Guniet came up with a WannaCry decryption tool which he aptly named WannaKey and is available for free download here. WannaKey strives at finding out the prime numbers used in the formula for generating the encryption keys. However, the same works only on Windows XP, said Guniet.
Guniet also said “It does so by searching for them in the wcry.exe process. This is the process that generates the RSA private key. The main issue is that the CryptDestroyKey and CryptReleaseContext does not erase the prime numbers from memory before freeing the associated memory.”
Considering how the decryption tool works; it is imperative to say that the files can only be retrieved with WannaKey only if:
- The PC has not been rebooted once attacked and infected.
- The associated memory has not been erased and allocated to other processes.
Based on Guinet’s findings, some other private cybersecurity organizations and researchers have able to design another tool that has broader applications.
Also Read: Android Malware “Judy” Infects 36.5 Million Users
WanaKiwi: WannaCry Ransomware Decryption Tool
Yet another security researcher Benjamin Delpy has developed another tool known as WanaKiwi. WanaKiwi is an easy to use tool which reduces the complexity of WannaCry-infected file decryption.
WannaCry victims can download this tool for free from WanaKiwi tool from Github. Once downloaded they should run the tool on their infected Windows PC using the command line.
Unlike WannaKey, WanaKiwi works on Windows XP, Windows 7, Windows Vista, Windows Server 2003 and 2008.
Matt Suiche, founder and CEO of Comae Technologies has also provided a series of demonstrations showing how to use WanaKiwi to decrypt your files.
While there still are chances that the tool doesn’t work owing its dependencies, victims still are advised to use these tools on their infected computers. At least it gives them some hope that their files will be unlocked.
Also Read: EternalRocks: A Malware More Lethal Than WannaCry Is Out




Leave a Reply