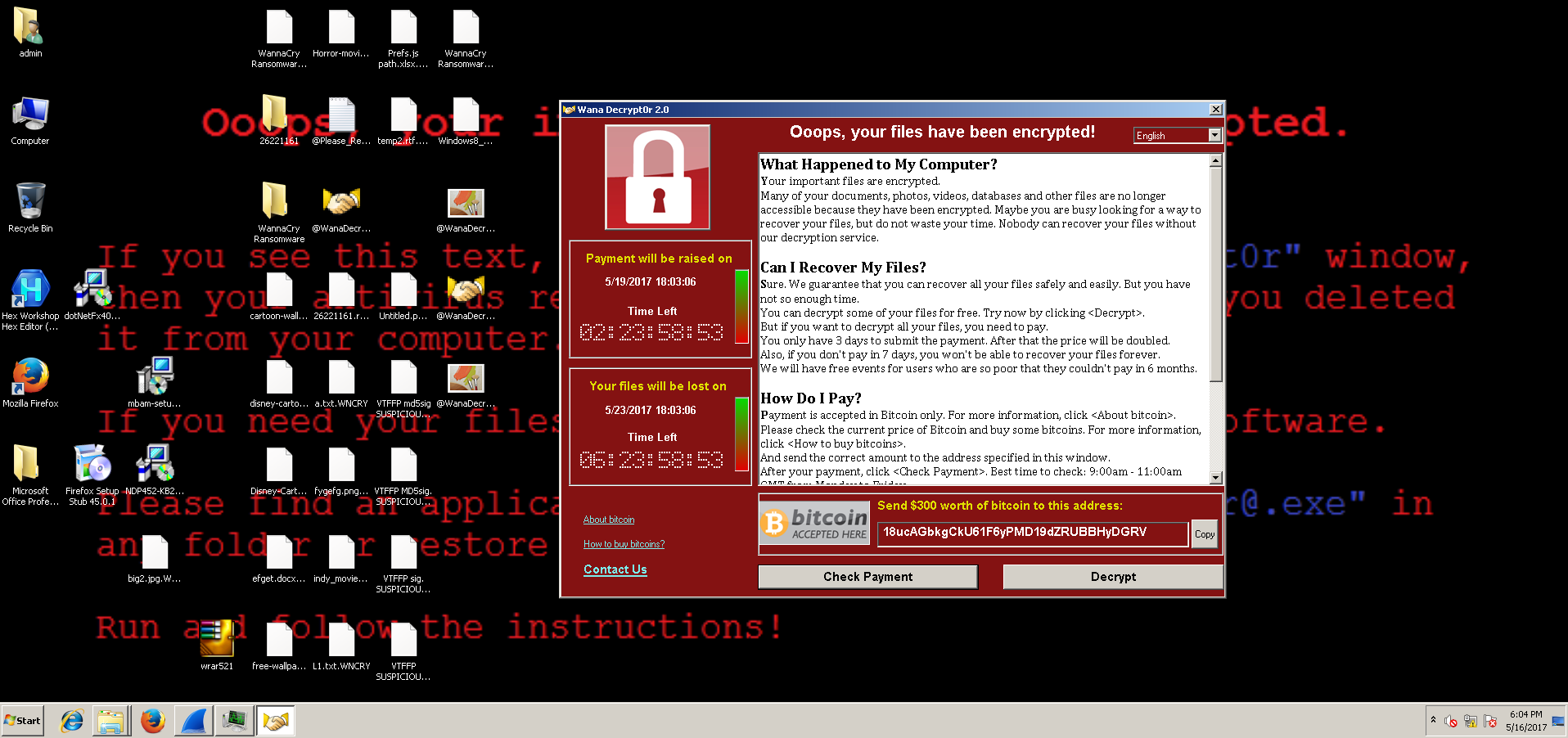
WannyCry mayhem doesn’t seem to be leaving us any soon. From medical institutions, government firms to different organizations on target, WannaCry cyberattack has hit them all hard. Computers across the globe have been left locked and are being demanded ransom.
What is WannaCry:
A piece of malware capable of taking over your computer control and preventing any kind of access until a ransom in form of bitcoins is paid in return.
How does WannaCry attack a computer?
A major cause of ransomware attacks is the inattentiveness of users while opening emails. Without being careful while opening emails having attachments or links, they easily get trapped. These emails are known as phishing emails and easily gets hold of such computers.
Once the computer has been attacked by WannaCry ransomware, it will encrypt all the files on your PC and the file extensions will be changed to “.wnry”.
Post this, users are demanded ransom in form of bitcoins, if not paid their data keeps on getting deleted at different time intervals.
Target Files:
.bz2, .mp4, .mkv, .zip, .rar, .tar, are the media archive file extension which are vulnerable for ransomware attacks.
.ppt, .doc, .docx, .sxi, .xlsx, are some of the commonly Microsoft Office file extensions that are targeted.
.sxw, .odt, .hwp, are some of the Office extension which are not so common but are in the target list.
.eml, .ost, .pst, .msg, .edb, are amongst the emails and email databases extensions that ransomware attacks.
.php, .cpp, .pas, .java, .asm, are the project files and source codes that ransomware attacks.
.key, .pfx, .pem, .p12, .csr, .gpg, .aes, lie under of the category of encryption keys and certificates that can be attacked by ransomware.
.accdb, .odb, .myd, .sql, .mdb, are some of the database files which are prone to ransomware attacks.
Virtual machine files such as .vmx, .vmdk, .vdi are also a major target for ransomware attacks.
Read Also: Android Malware “Judy” Infects 36.5 Million Users
Preventive measures:
- Patches released by Microsoft Security Bulletin MS17-010 should be installed on priority.
- Organizations and firms which use Enterprise Edge or perimeter network devices [UDP 137, 138 and TCP 139, 445] to connect to the Internet, should immediately disable SMBv1 or block their SMB ports.
- Users having older versions of Windows such as XP, Vista, Windows Server 2003 and 2008 should update the Operating Systems without any further delay.
- Frequent backup of data should be performed and the backup should also be saved on different devices.
- An updated antivirus application should always be used.
- Be wary while opening attachments and links in emails. It is advised to be cautious while opening attachments and links in suspicious and unsolicited e-emails, even from known contacts. It is advised not to open emails with unusual extension names such as .ecc, .vvv, .micro, .OMG!, .CTBL, .crypto, .micro, .r5a, .vault, .good etc.
- Firewalls should be enabled on individual workstations.
Also Read: WannaCry Ransomware Attack, Here’s All You Should Know About It!
What to do when your PC is infected with WannaCry?
- Never pay the ransom demanded from the attackers. Even paying ransom nowhere guarantees that your information and files will be released.
- All the external storage and all kind of network connections should immediately by disconnected.
- The data can be recovered if you have data backups. However before recovering the data, WannaCry infection should be removed using a reputable anti-virus/malware application.
Conclusion:
As is said prevention is better than cure, rather than being a victim of such attacks using some simple steps you can save yourself from such situations.
Read Also: Finally, There’s a Way To Get Back Your Locked Files: WannaCry Decryptor Tool Released & Its Free






Leave a Reply